PKOS 1주차 - AWS kOps 설치 및 기본 사용
PKOS - Production Kubernetes Online Study 포스팅을 시작하며
PKOS 1주차 - AWS kOps 설치 및 기본 사용
PKOS 4주차 - Harbor & Gitlab & ArgoCD
PKOS 5주차 - Prometheus & Grafana
PKOS 6주차 - Alert Manager & Logging System
왜 그런지 모르겠는데 이미지 위아래로 여백이 생깁니다.
에디터에서는 안그러는데 왜 그런지 좀 찾아봐야겠습니다.
본 글은 초안이기에 다듬는 과정에서 내용이 수정될 수 있습니다.
PKOS 1주차
들어가기전에
본 내용은 CloudNet@ 팀에서 진행하는 쿠버네티스 실무 실습 스터디를 기반으로 작성된 내용입니다.
1주차에는 Kubernetes Operations(이하 kOps), Helm을 설치하고 간단 실습을 진행했습니다.
kOps 실습 마지막에는 CLB(Classic Load Balancer)를 이용해 마리오 게임을 배포했습니다.
- CLB는 2022년 08월 15일에 사용 중지될 예정입니다.1
- EC2-Classic 서비스 중단 예정 및 대비 방법 공지 - https://aws.amazon.com/ko/blogs/korea/ec2-classic-is-retiring-heres-how-to-prepare/
- Classic Load Balancer 마이그레이션 - https://docs.aws.amazon.com/ko_kr/elasticloadbalancing/latest/userguide/migrate-classic-load-balancer.html
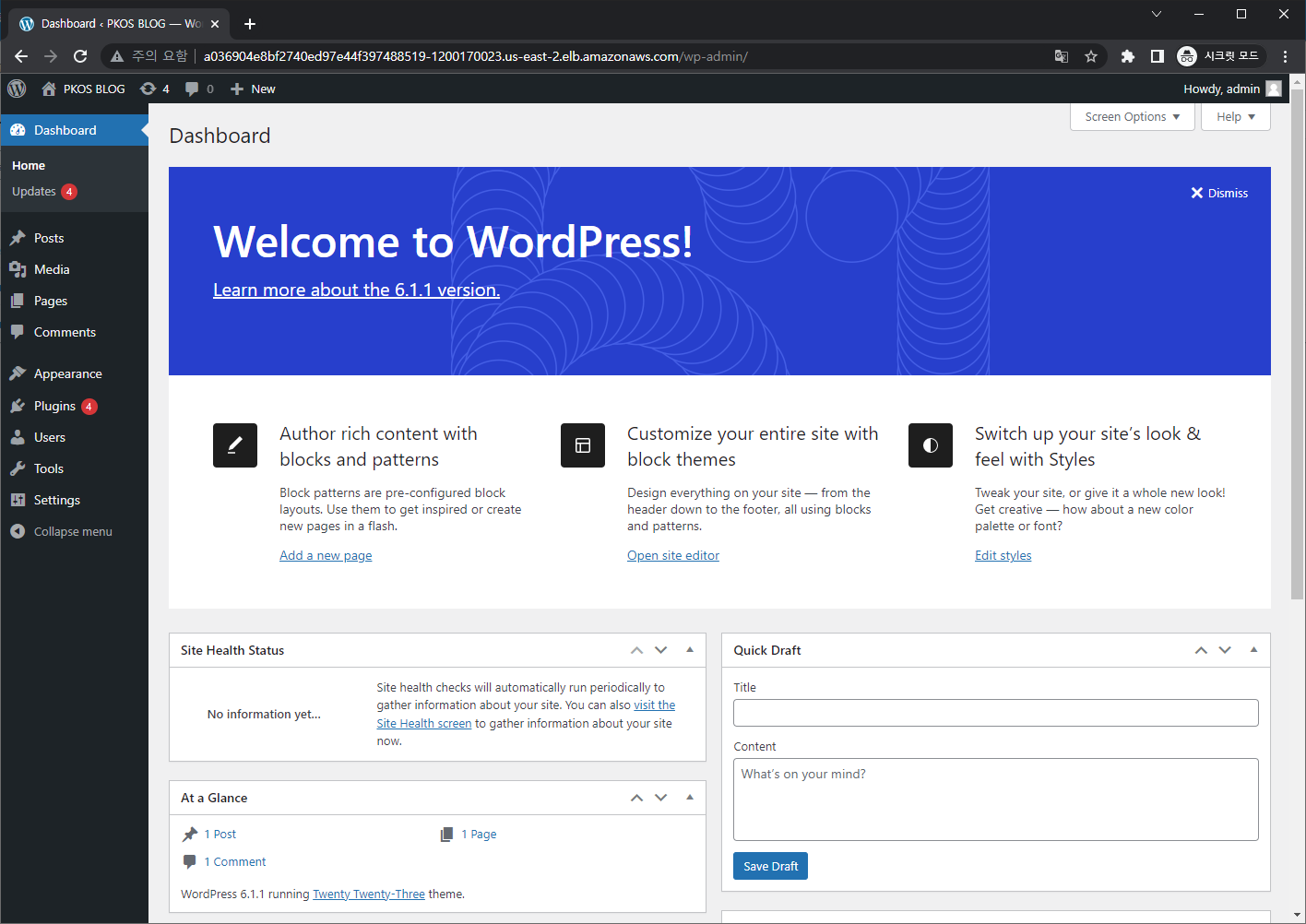
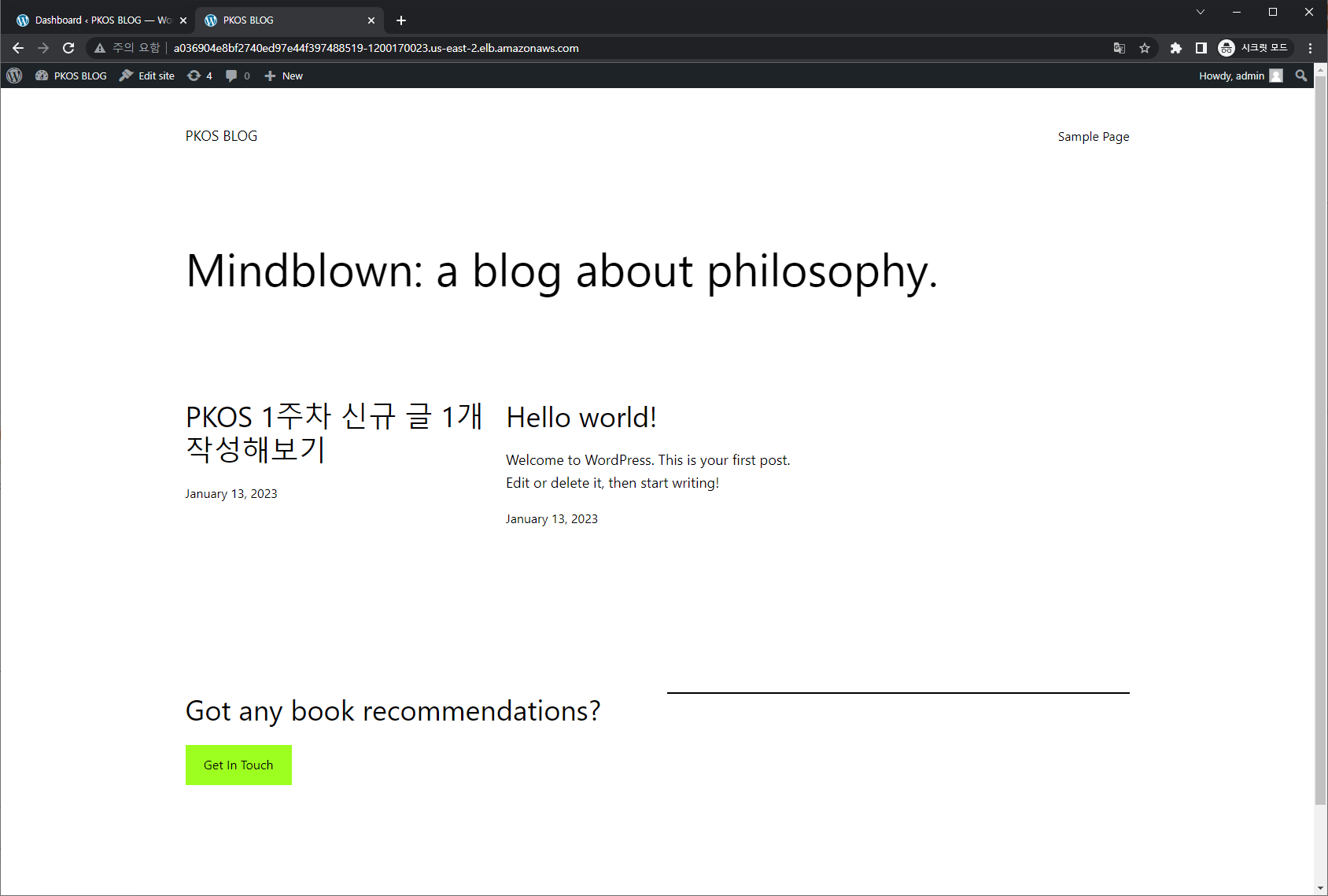
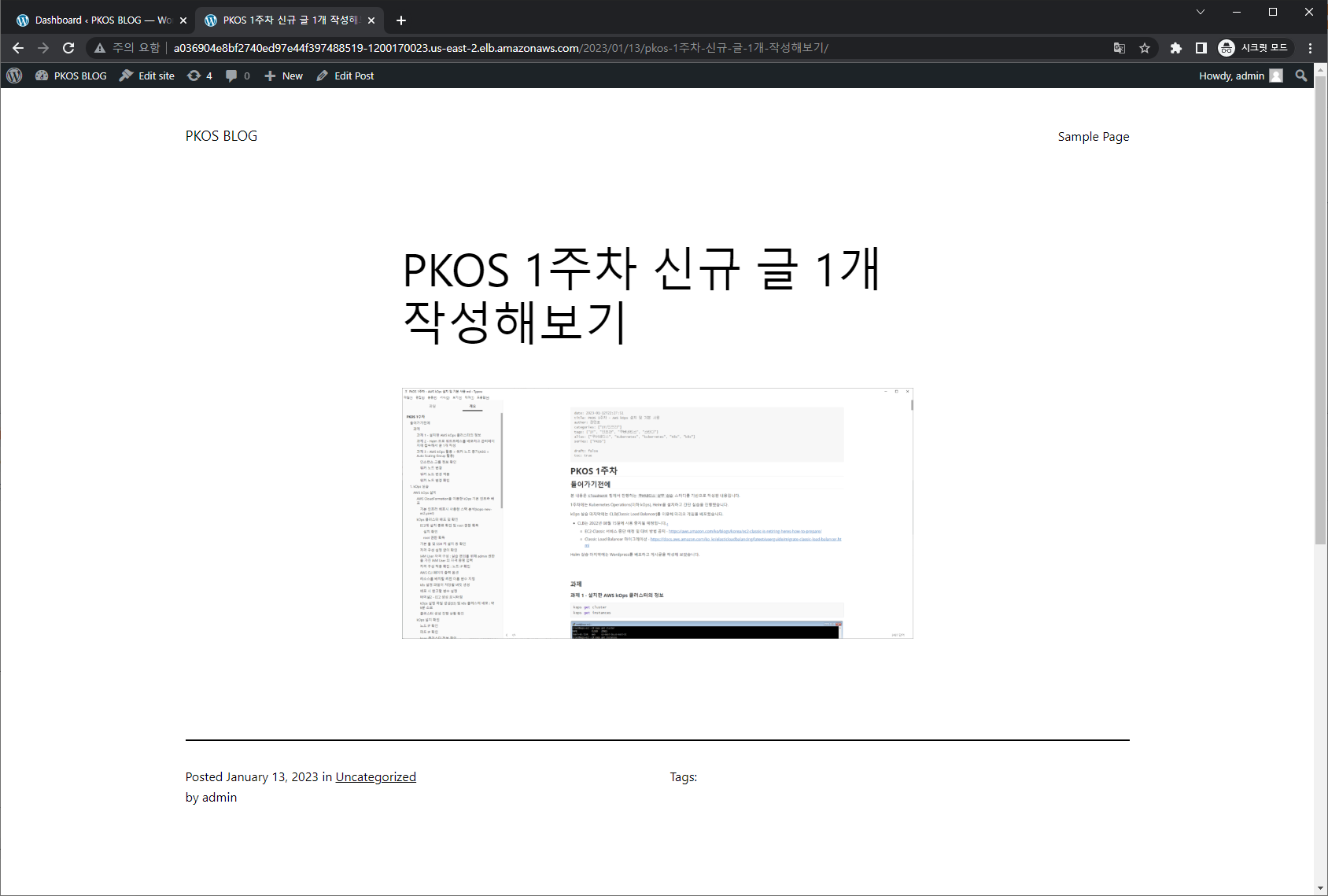
Helm 실습 마지막에는 Wordpress를 배포하고 게시글을 작성해 보았습니다.
과제
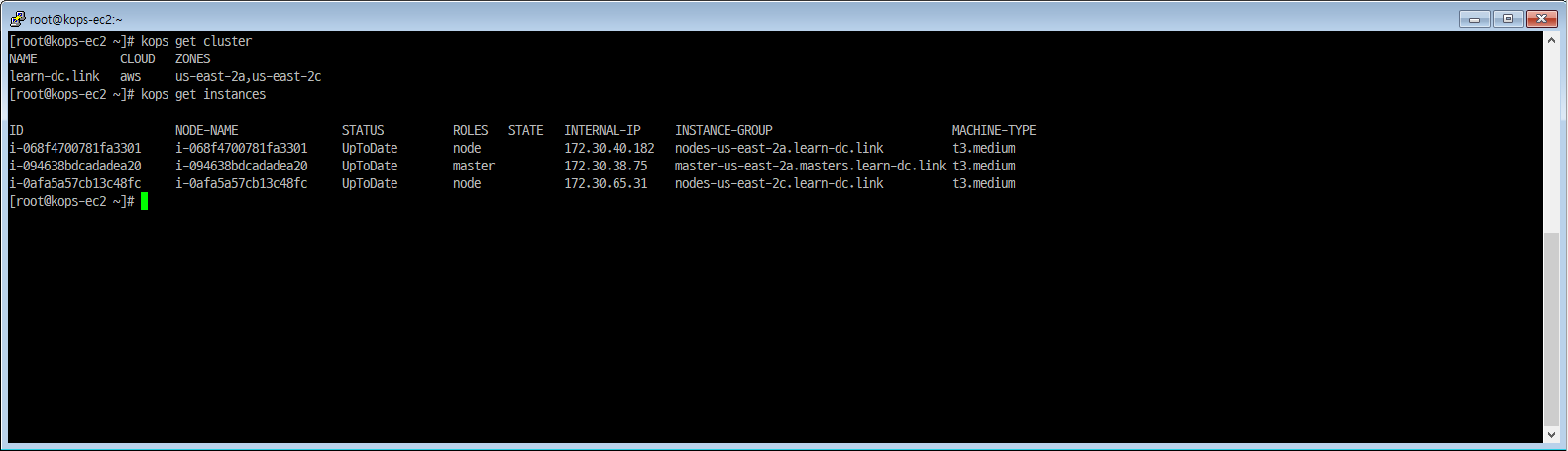
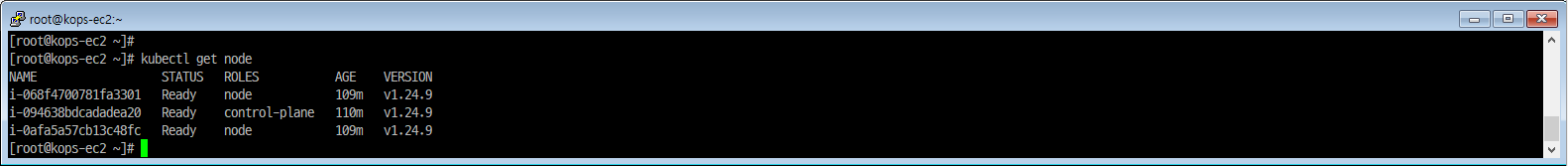
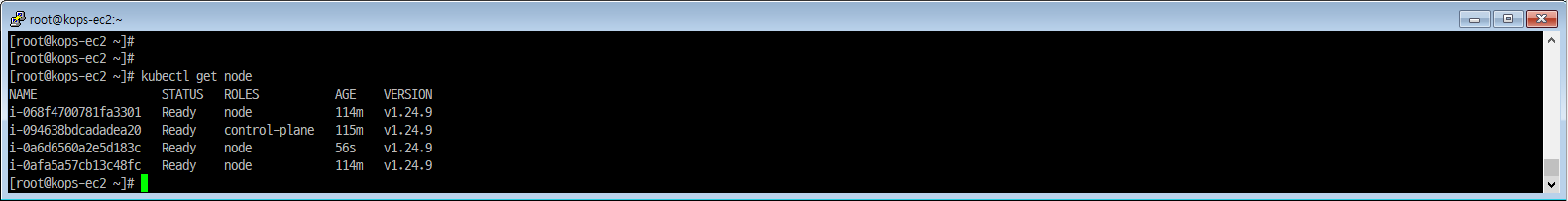
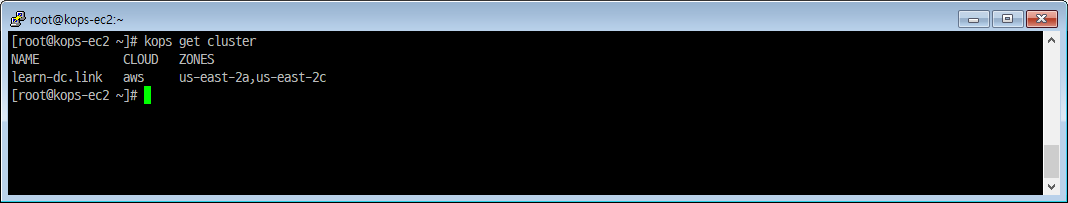
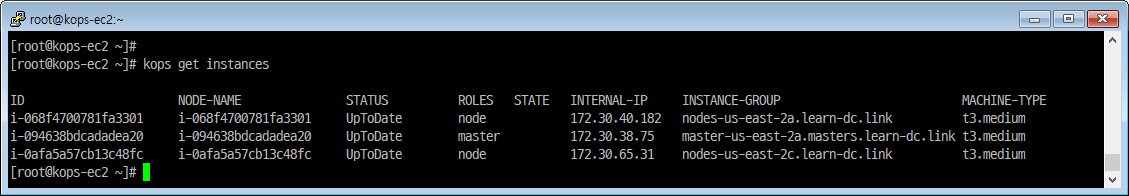
과제 1 - 설치한 AWS kOps 클러스터의 정보
|
|
과제 2 - Helm 으로 워드프레스를 배포하고 관리페이지에 접속해서 글 1개 작성
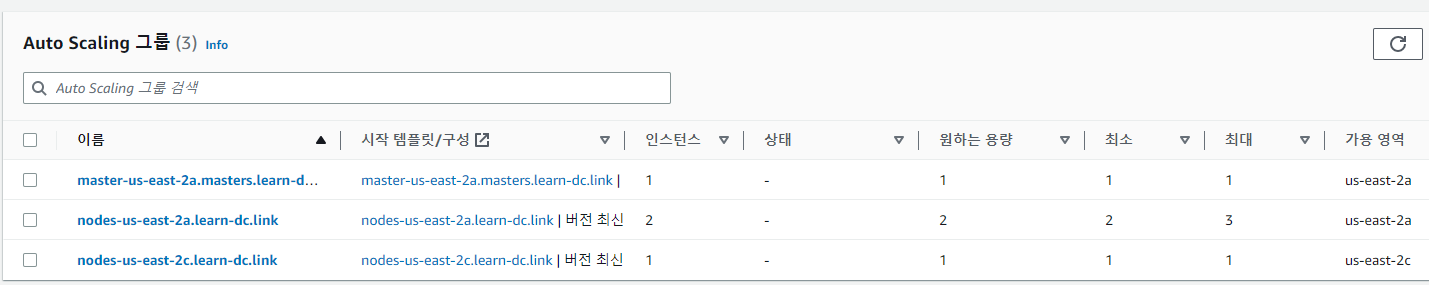
과제 3 - AWS kOps 활용 > 워커 노드 증가(ASG = Auto Scaling Group 활용)
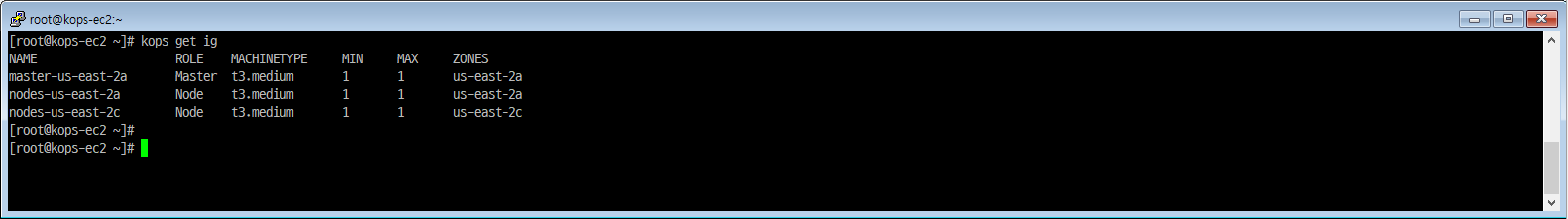
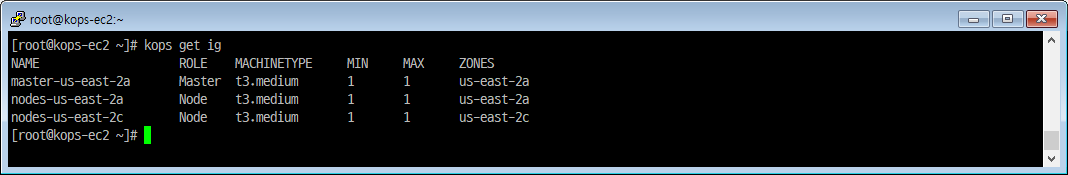
인스턴스 그룹 정보 확인
|
|
|
|
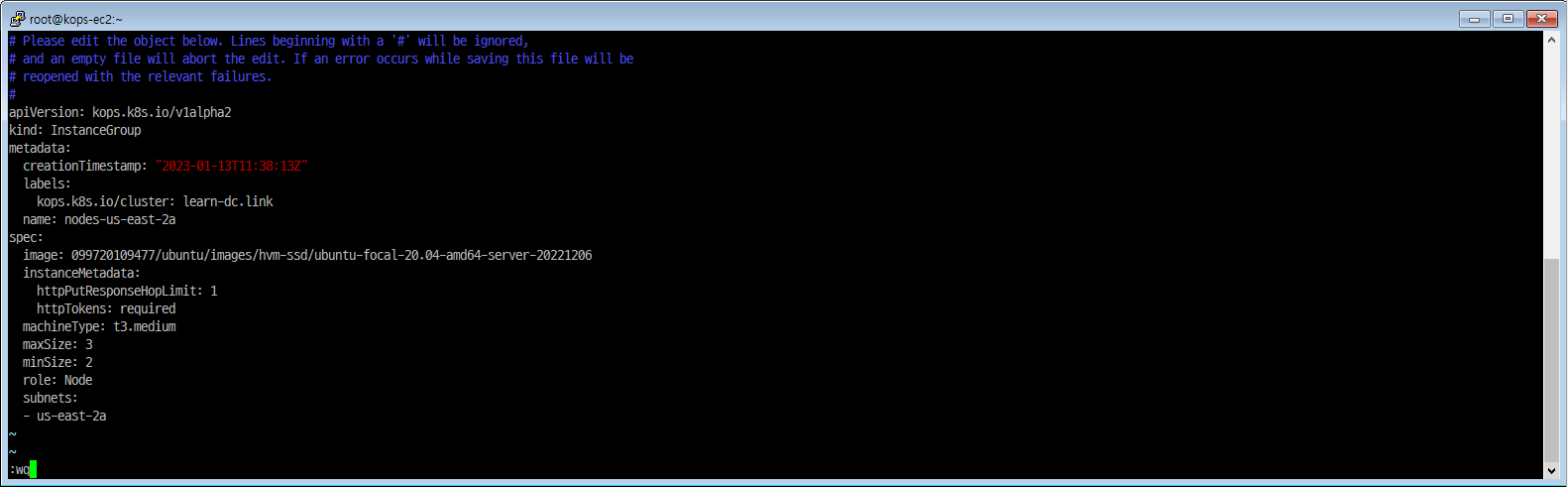
워커 노드 변경
|
|
- maxSize: 0 -> 3
- minSize: 0 -> 2
워커 노드 변경 적용
|
|
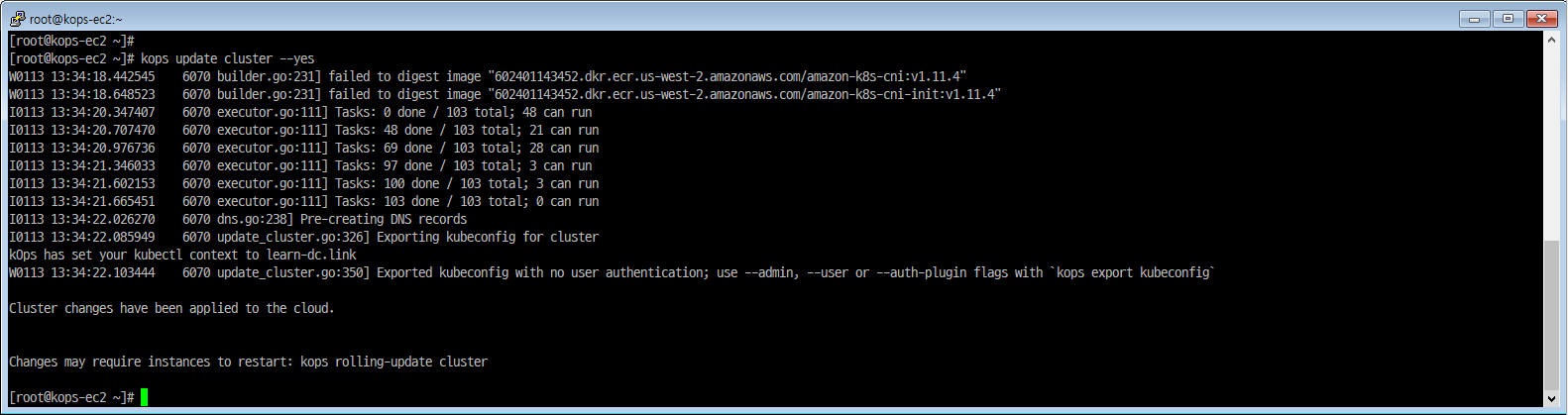
|
|
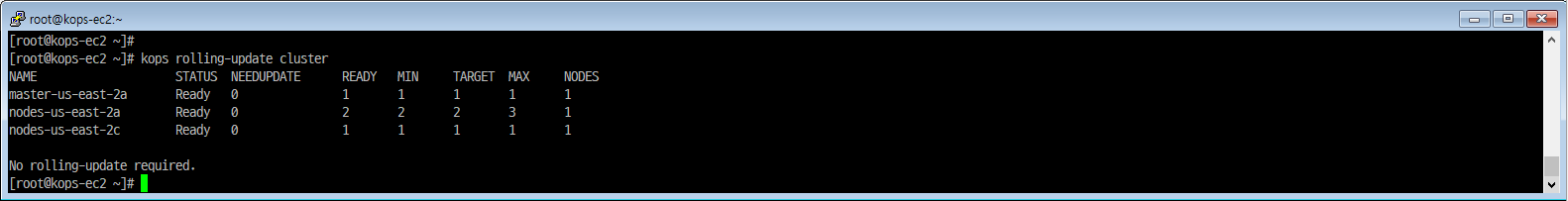
워커 노드 변경 확인
|
|
1. kOps 실습
AWS kOps 설치
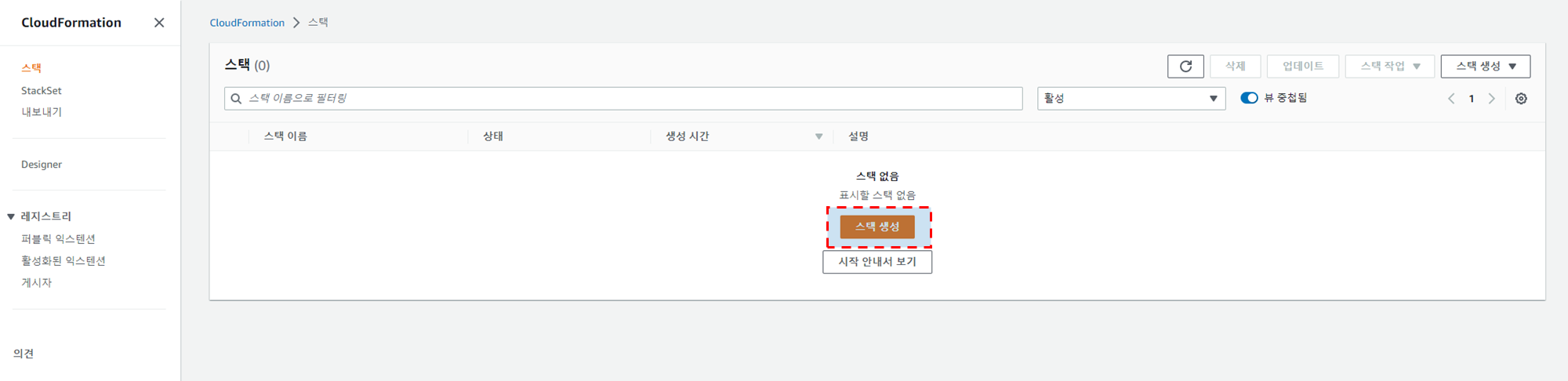
AWS CloudFormation을 이용한 kOps 기본 인프라 배포
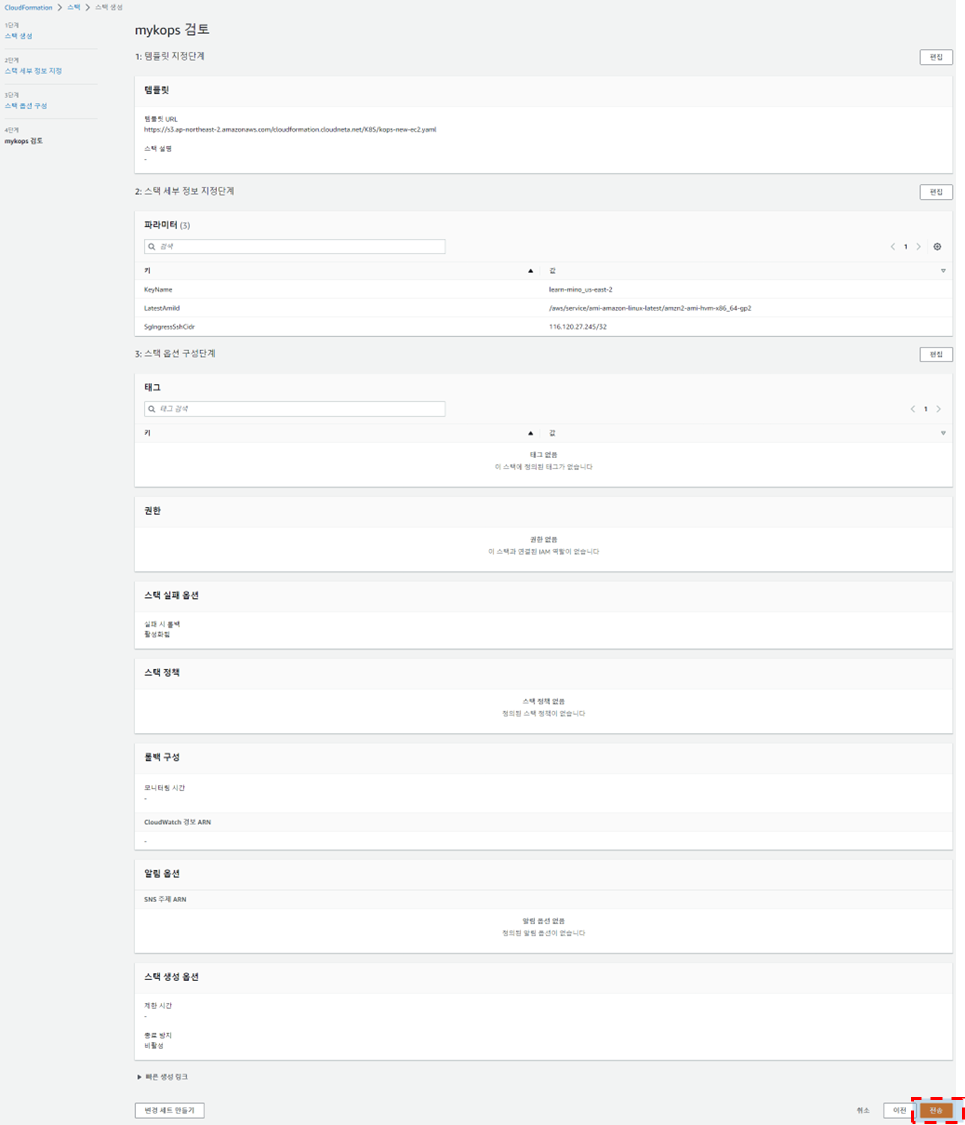
AWS CloudFormation 접속 후 안내에 따라 4단계를 거쳐 스택을 생성합니다.
- 스택 생성
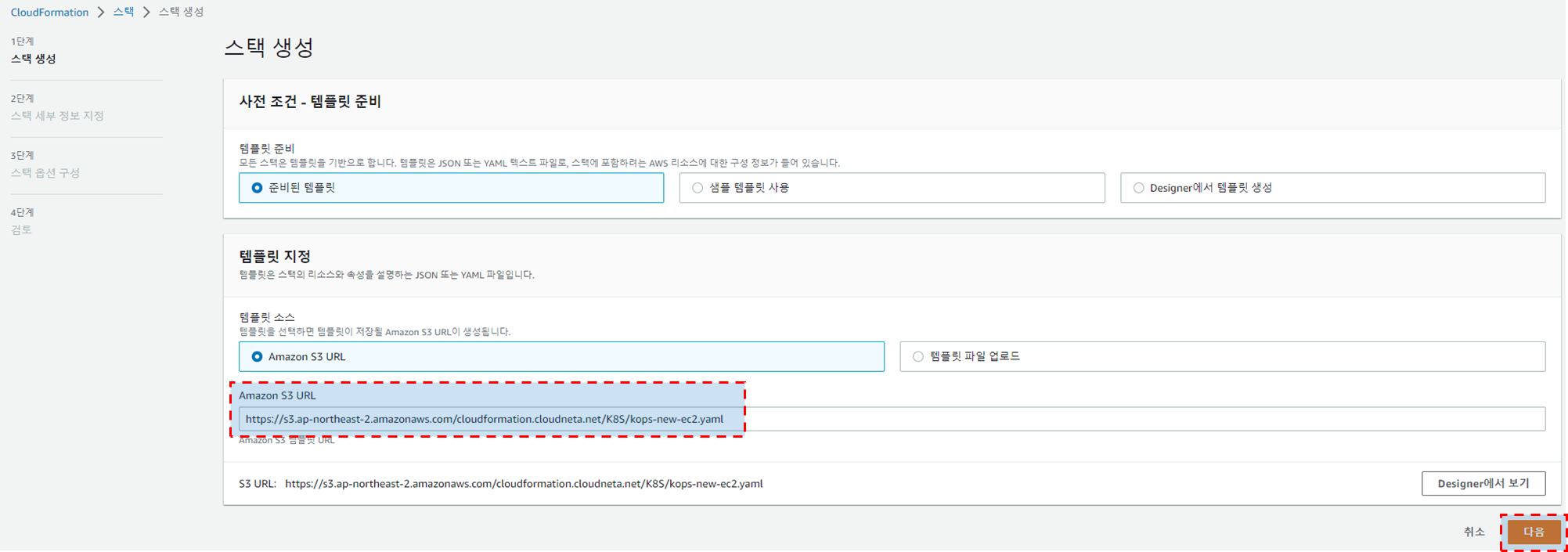
- 사전 조건 - 템플릿 준비
- 준비된 템플릿
- 템플릿 지정
- 템플릿 소스
- Amazon S3 URL
- Amazon S3 URL
- 템플릿 소스

- 사전 조건 - 템플릿 준비
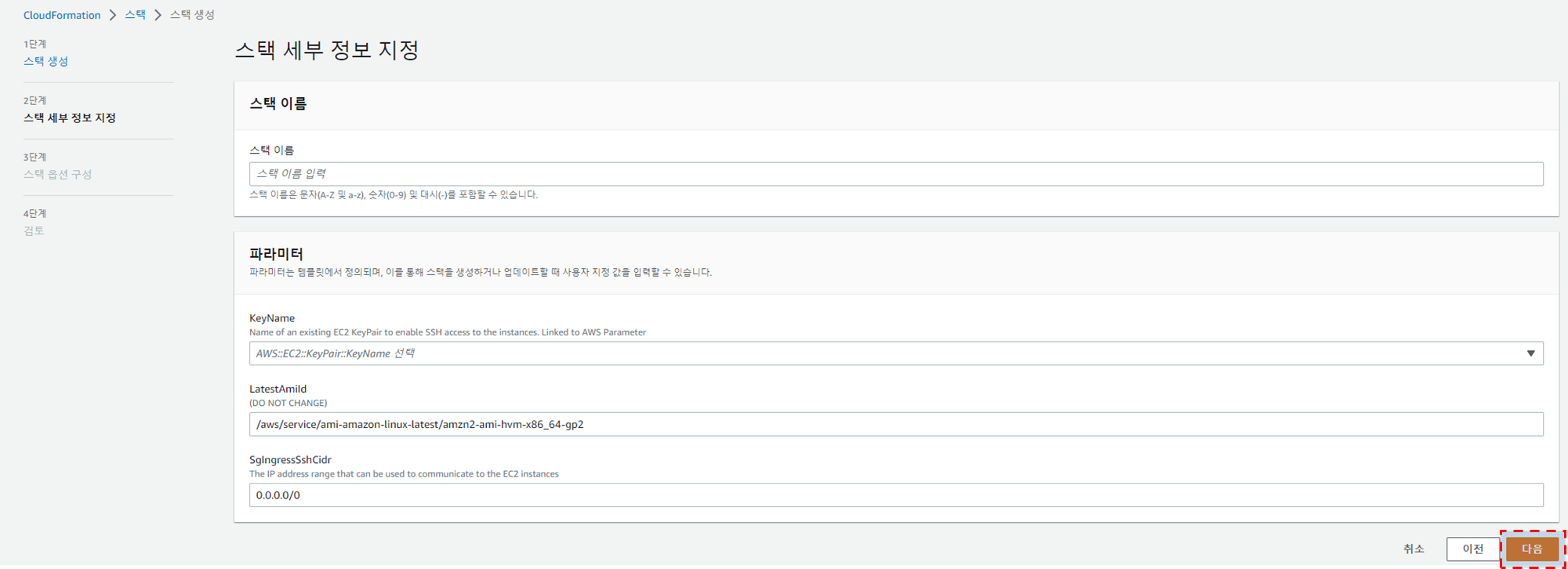
- 스택 세부 정보 지정
- 스택 이름
- 스택이름 : 사용자임의지정
- 파라미터
- keyName : 사용자임의지정; 사용자가 사용할 keypair 선택
- LatestAmild : 수정하지말것
- SgIngressSshCidr : : 사용자임의지정; SSH 접속시 사용할 IP 허용대역 입력

- 스택 이름
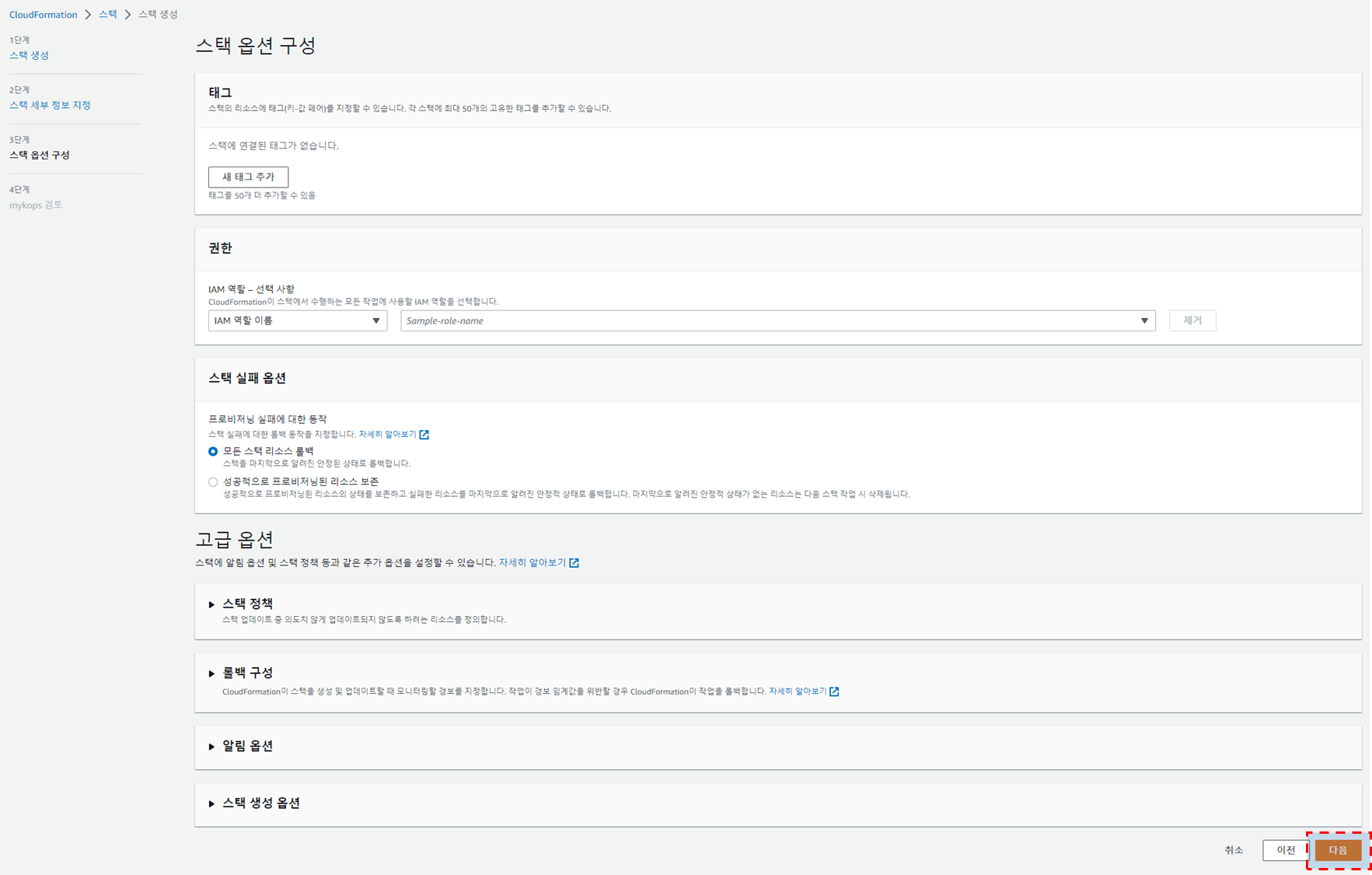
- 스택 옵션 구성
- 기본 항목 그대로
다음진행 
- 기본 항목 그대로
- 검토
- 기본 항목 그대로
전송진행 
- 기본 항목 그대로
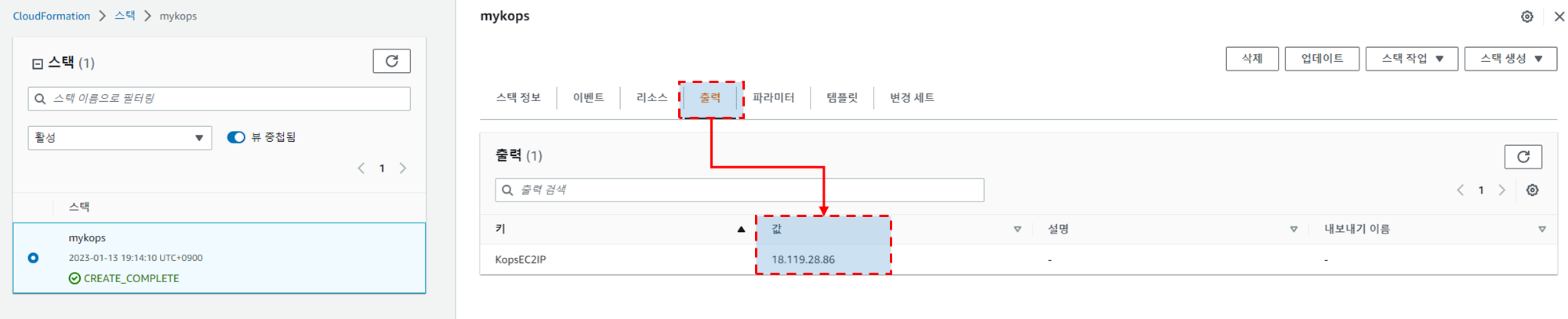
- 생성완료 및 EC2 접속 IP 확인 후 접속
- EC2 접속 IP 확인
- 출력
- 값 : 18.119.28.86
- Public IP 로 되도록 외부 노출에 주의합니다.

- 값 : 18.119.28.86
- 출력
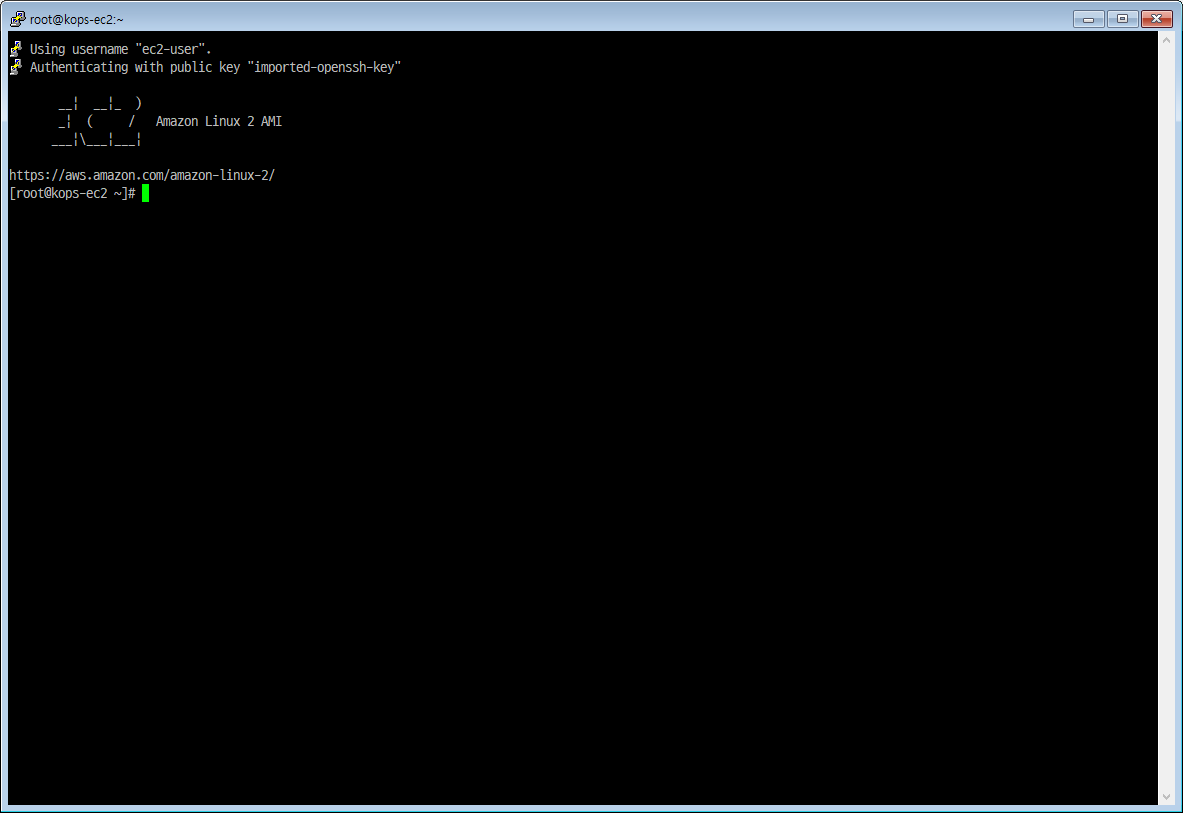
- EC2 접속
- EC2 접속 IP 확인
기본 인프라 배포시 사용한 스택 분석(kops-new-ec2.yaml)
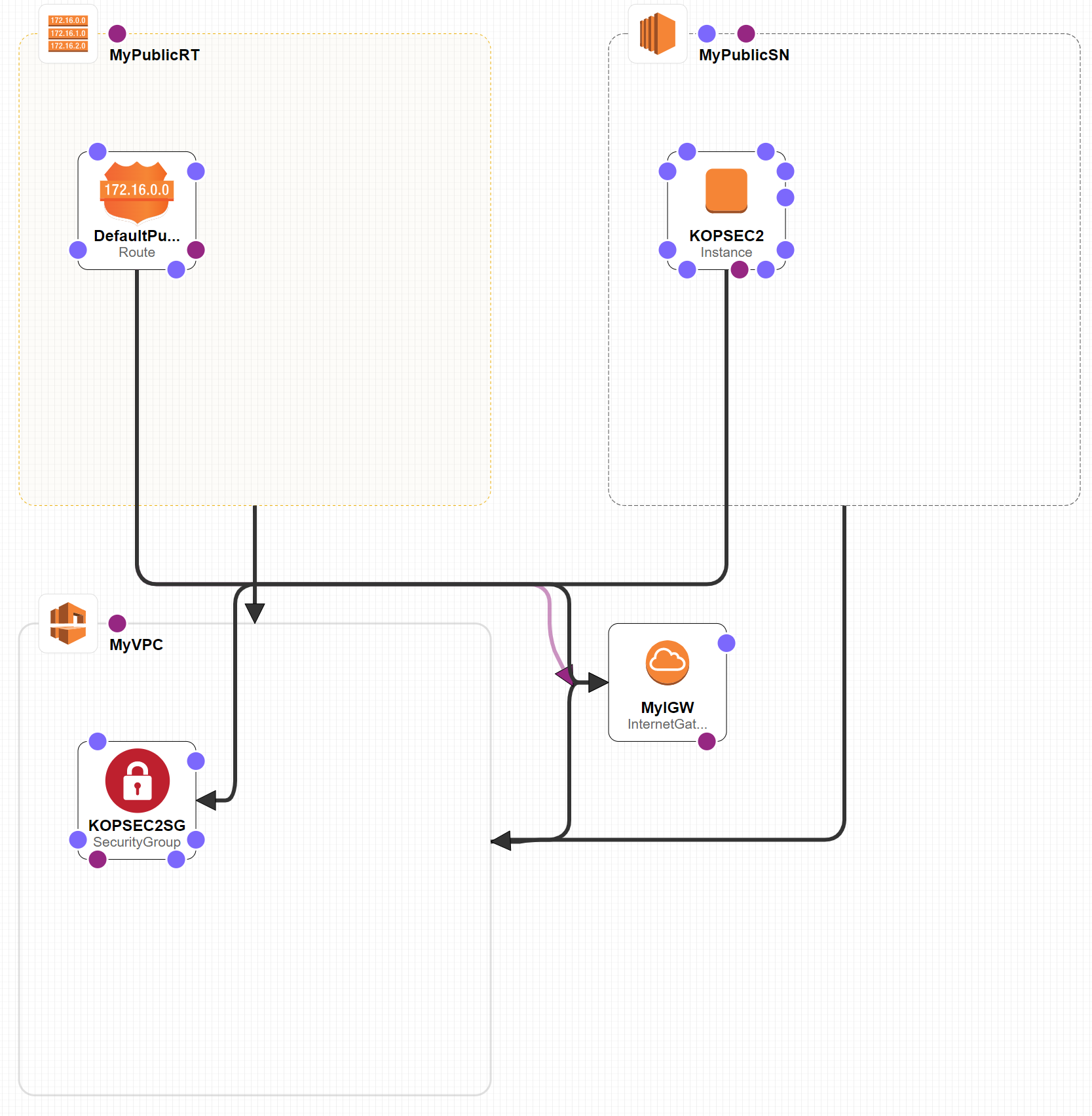
|
|
kOps 클러스터 배포 및 확인
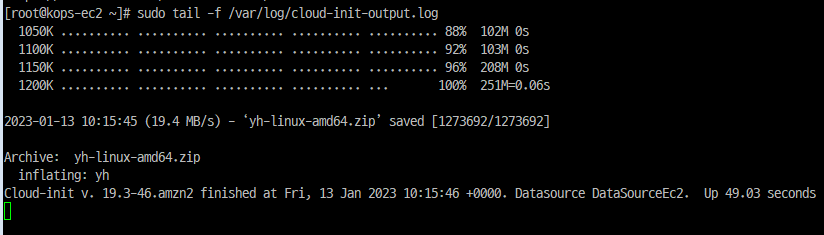
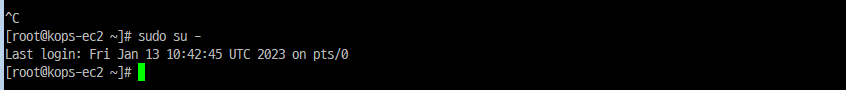
EC2에 설치 종료 확인 및 root 권한 획득
설치 확인
|
|
root 권한 획득
|
|
기본 툴 및 SSH 키 설치 등 확인
|
|
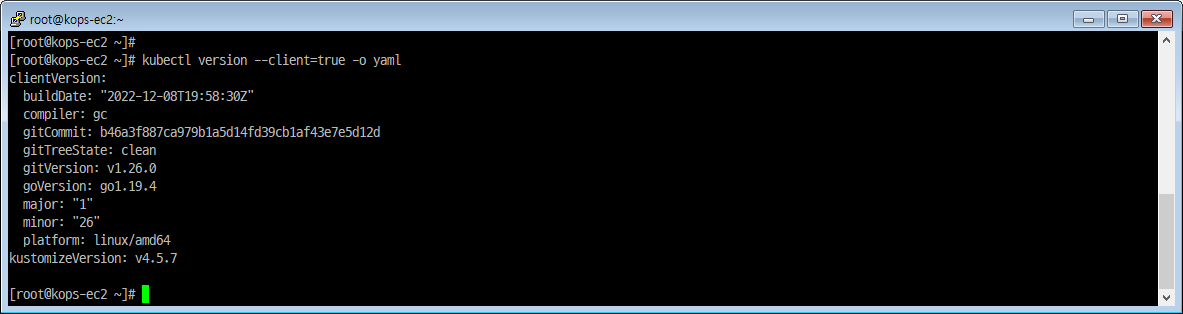
|
|
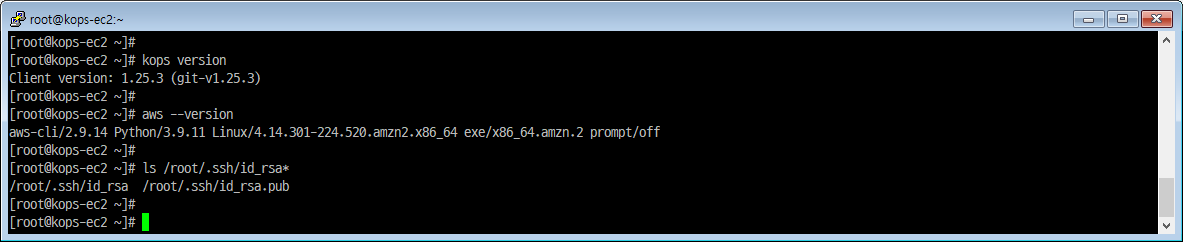
자격 구성 설정 없이 확인
|
|
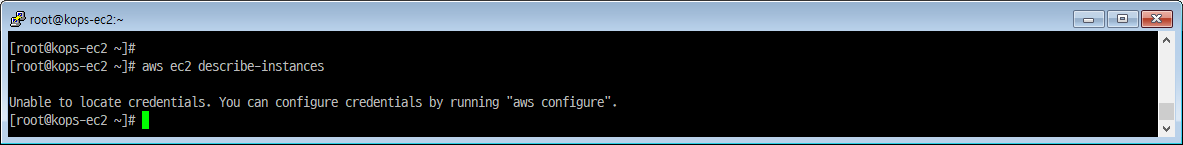
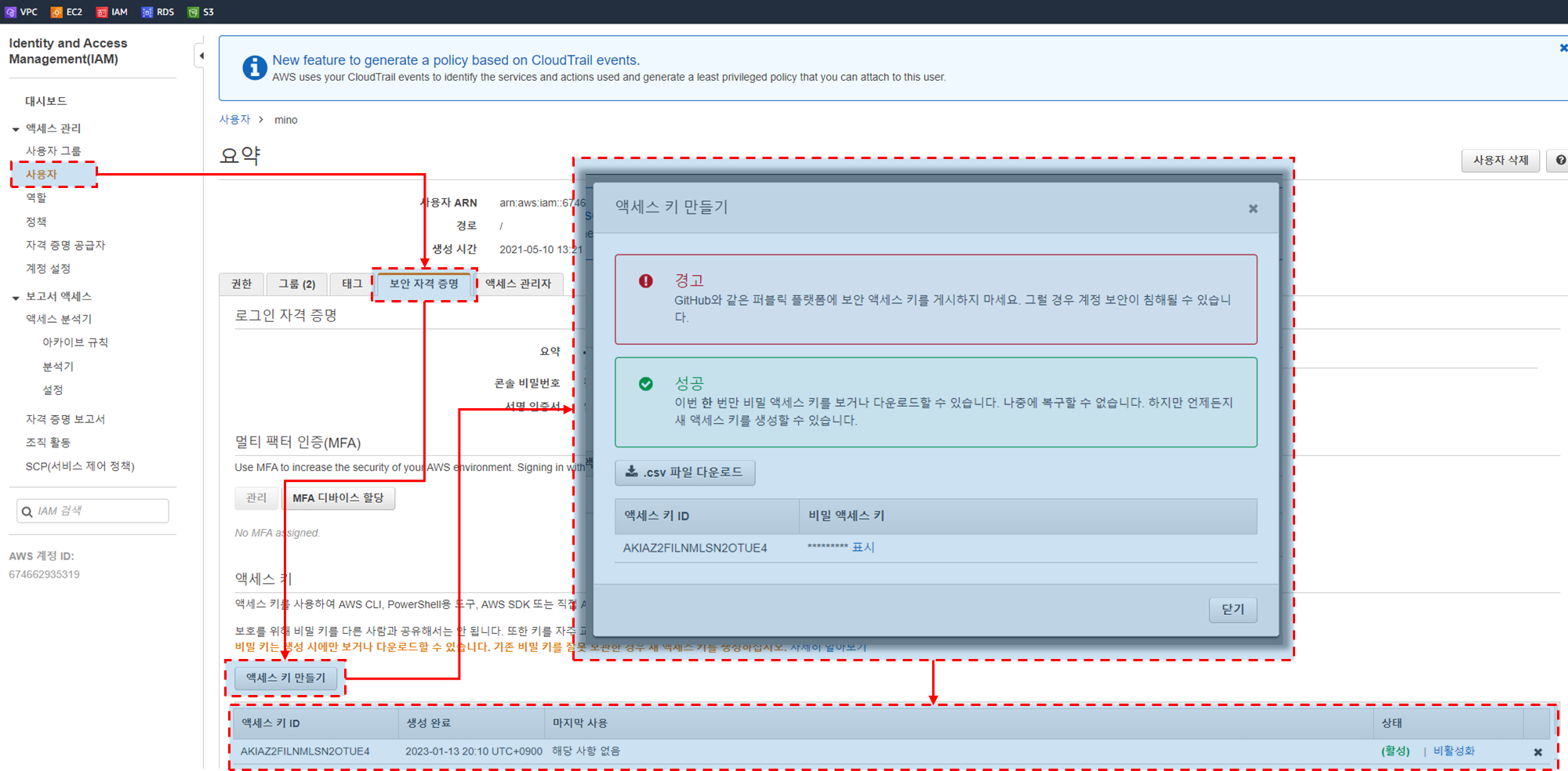
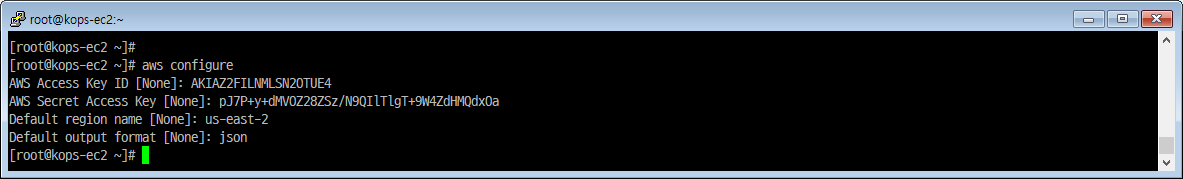
IAM User 자격 구성 : 실습 편의를 위해 admin 권한을 가진 IAM User 의 자격 증명 입력
|
|
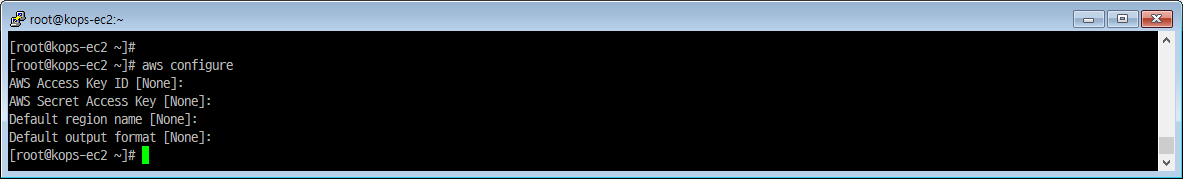
-
aws configure 설정 정보
- AWS Access Key ID [None]:
- IAM 에서 발급한 사용자 Access Key ID 입력
- AWS Secret Access Key [None]:
- IAM 에서 발급한 사용자 Secret Access Key 입력
- Default region name [None]: us-east-2
- 현재 사용중인 리전값 입력
- Default output format [None]: json
- AWS Access Key ID [None]:
-
IAM Access Key 발급
-
aws configure 설정
자격 구성 적용 확인 : 노드 IP 확인
|
|
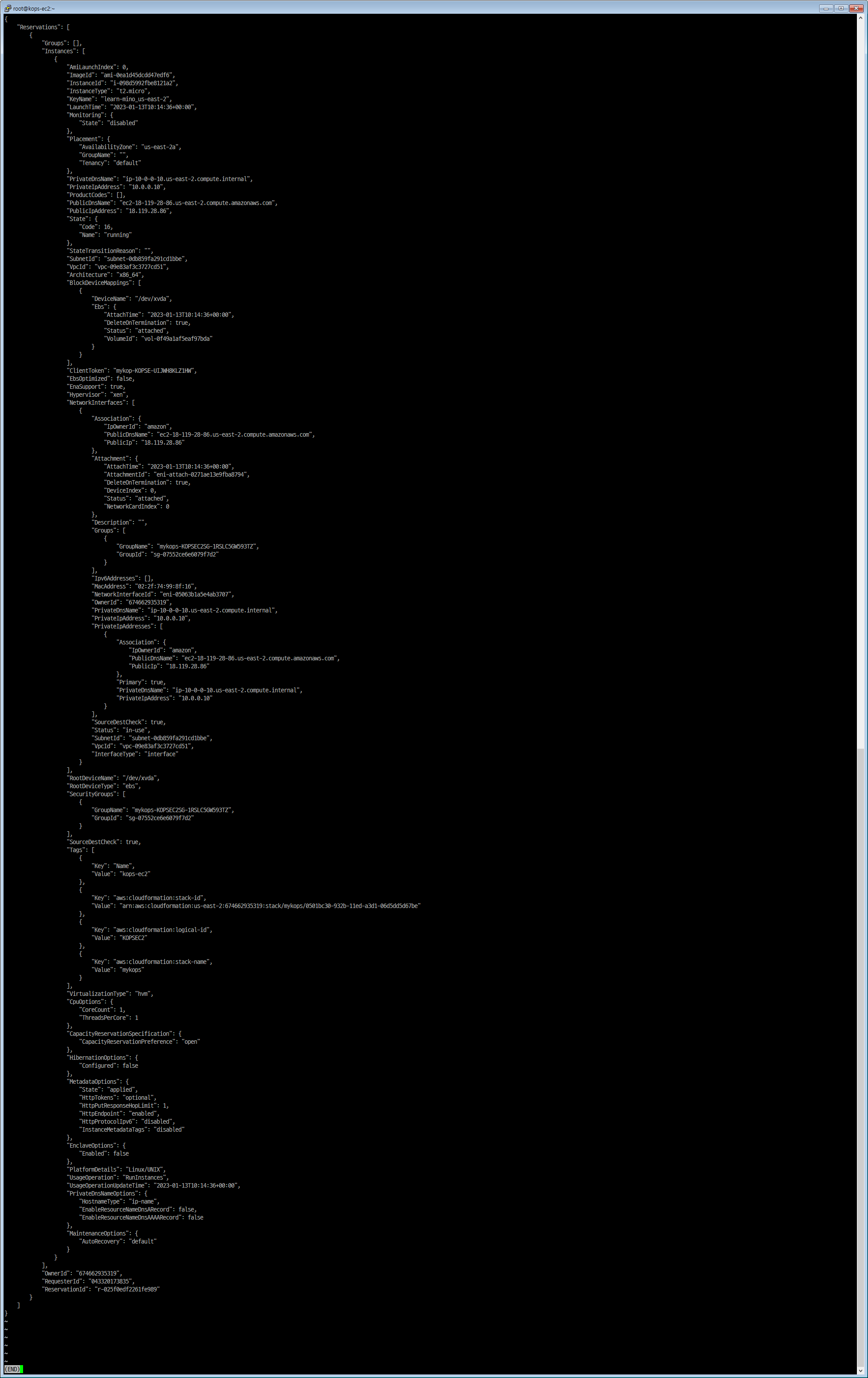
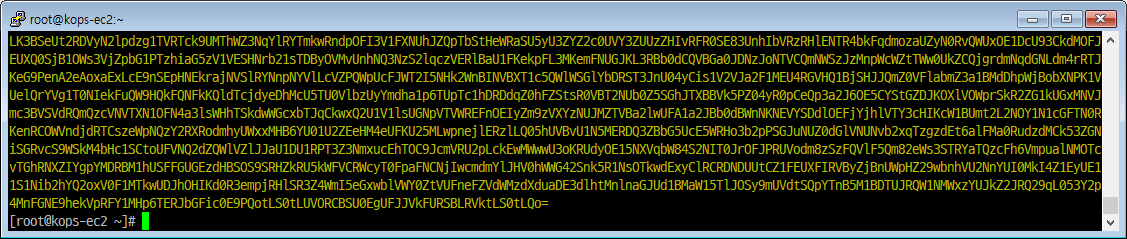
- 정보 전문
|
|
AWS CLI 페이지 출력 옵션
|
|
리소스를 배치할 리전 이름 변수 지정
|
|
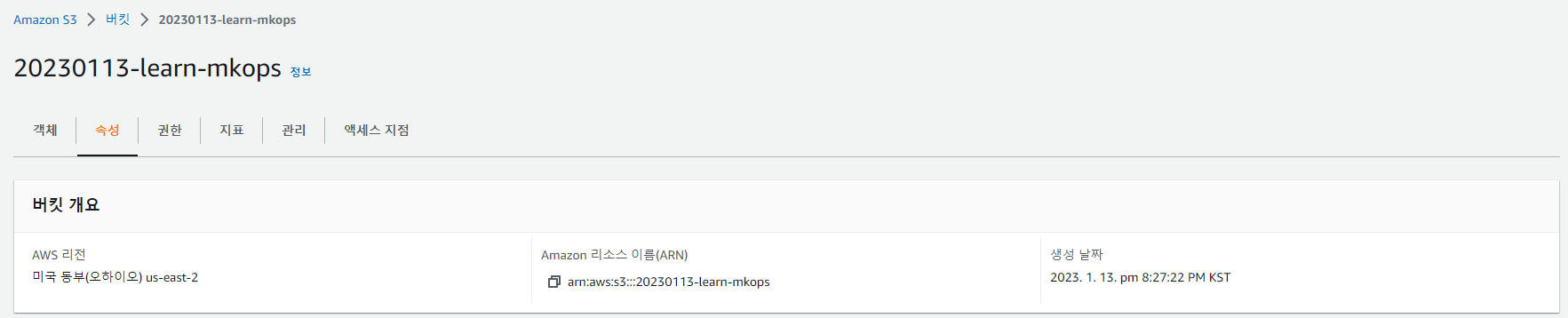
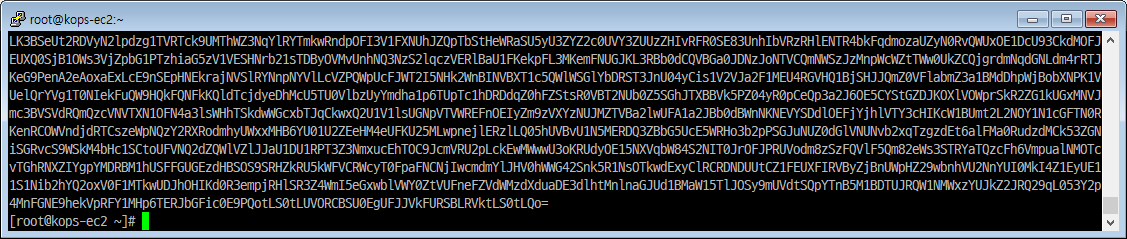
k8s 설정 파일이 저장될 버킷 생성
- aws s3 mb s3://버킷<유일한 이름> –region <S3 배포될 AWS 리전>
|
|
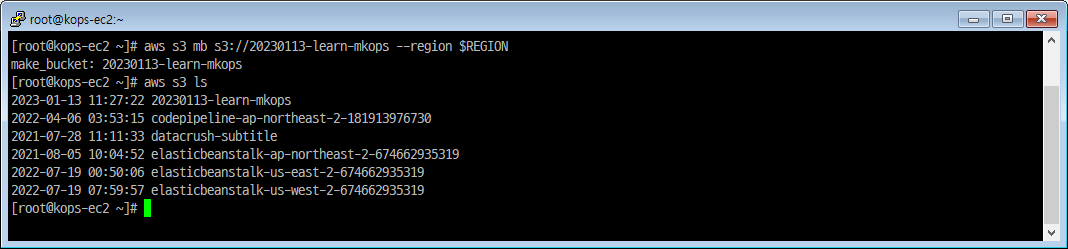
- 생성된 버킷
배포 시 참고할 변수 설정
- export KOPS_CLUSTER_NAME=<자신의 퍼블릭 호스팅 메인 주소>
- export KOPS_STATE_STORE=<s3://(위에서 생성한 자신의 버킷 이름)>
- export AWS_PAGER=""
- export REGION=<현재 사용하고 있는 리전>
|
|
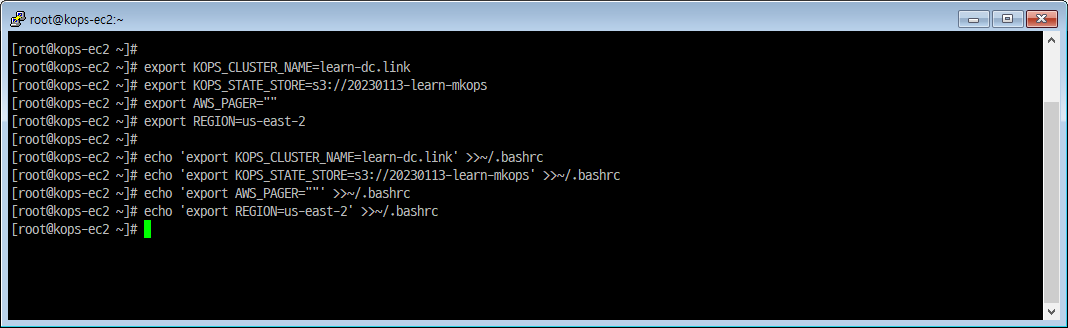
터미널2 - EC2 생성 모니터링
|
|
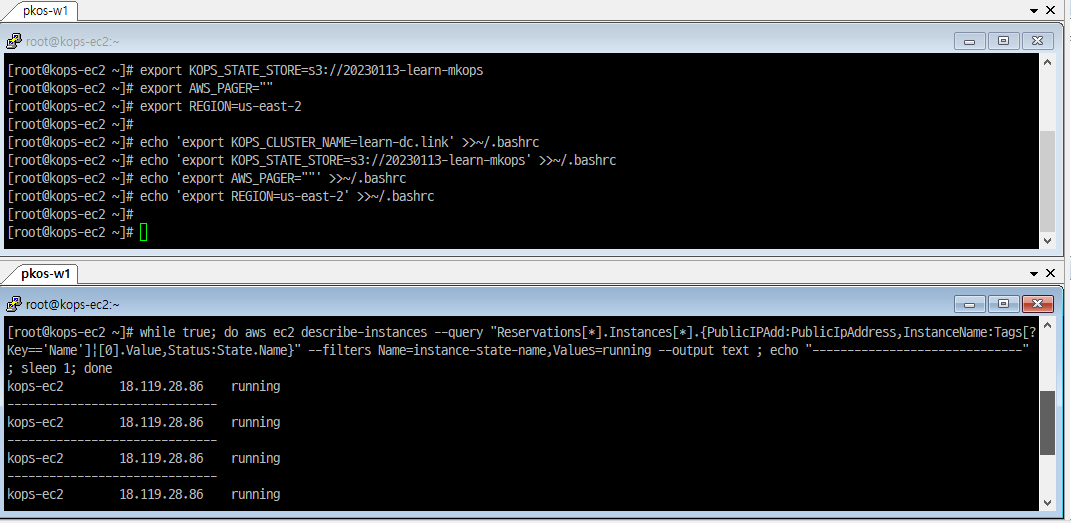
kOps 설정 파일 생성(S3) 및 k8s 클러스터 배포 : 약 6분 소요
- CNI(Container Networking Interface)는 AWS VPC CNI 사용
- 1대(t3.medium) - 마스터 노드
- 2대(t3.medium) - 워커 노드
- 파드 사용 네트워크 대역 지정(172.30.0.0/16; 172.30.0.0~172.30.255.255)
|
|
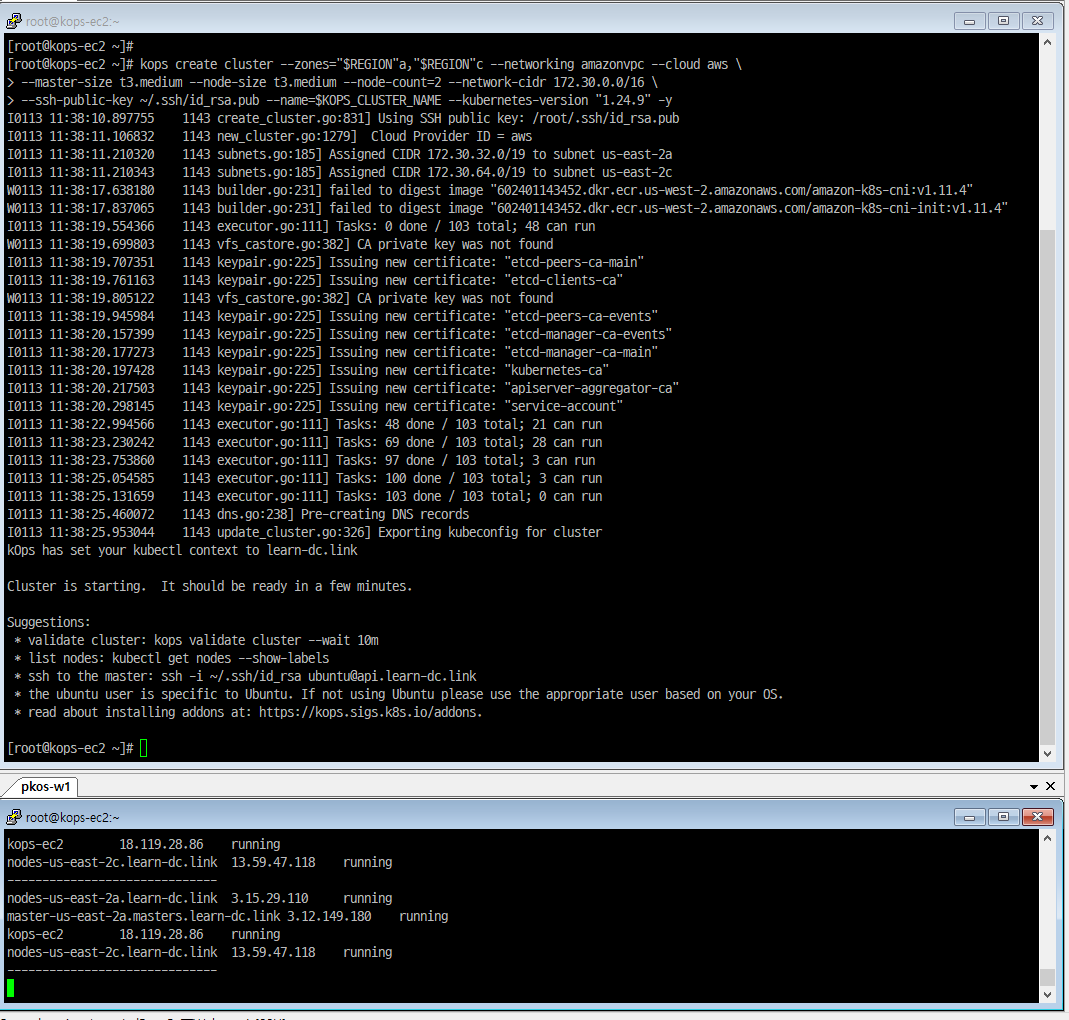
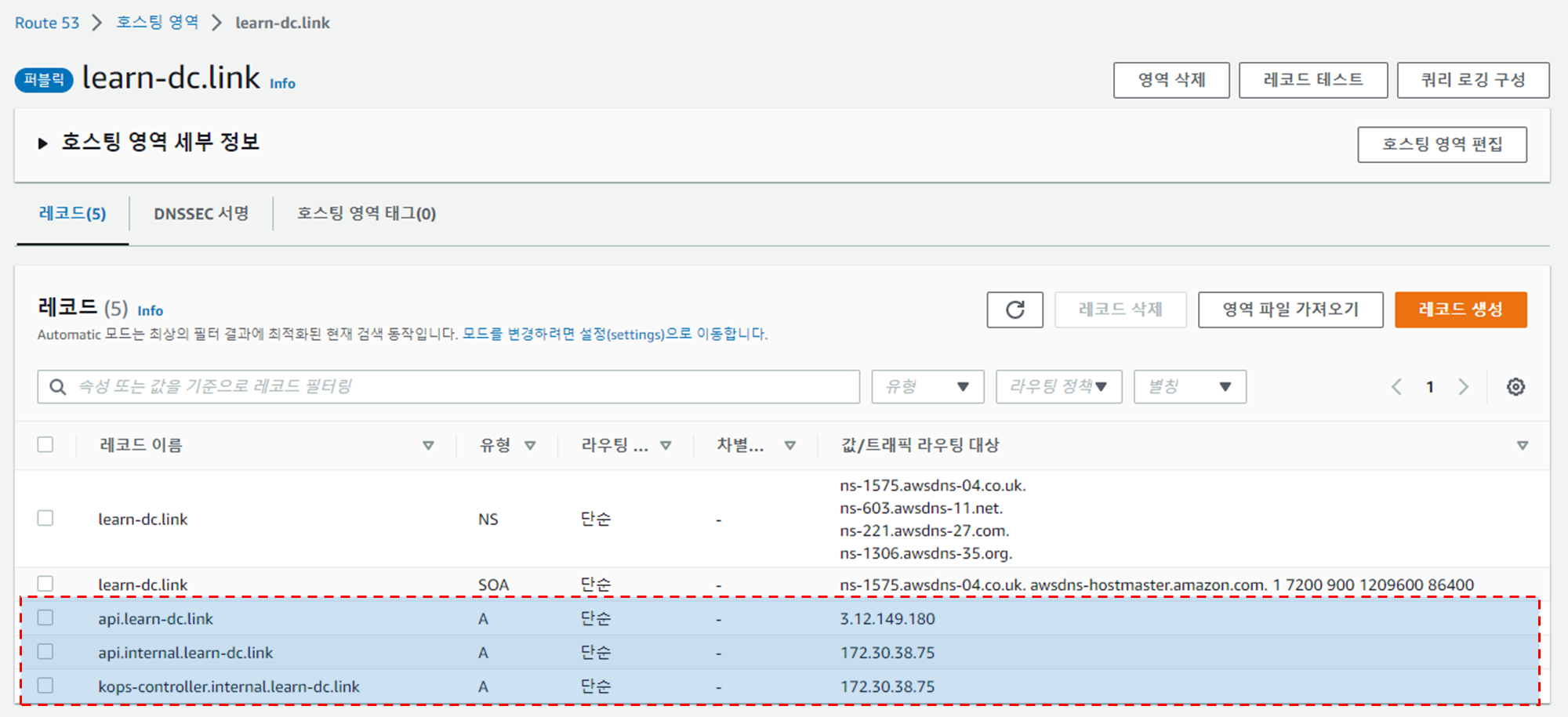
클러스터 생성 진행 상황 확인
|
|
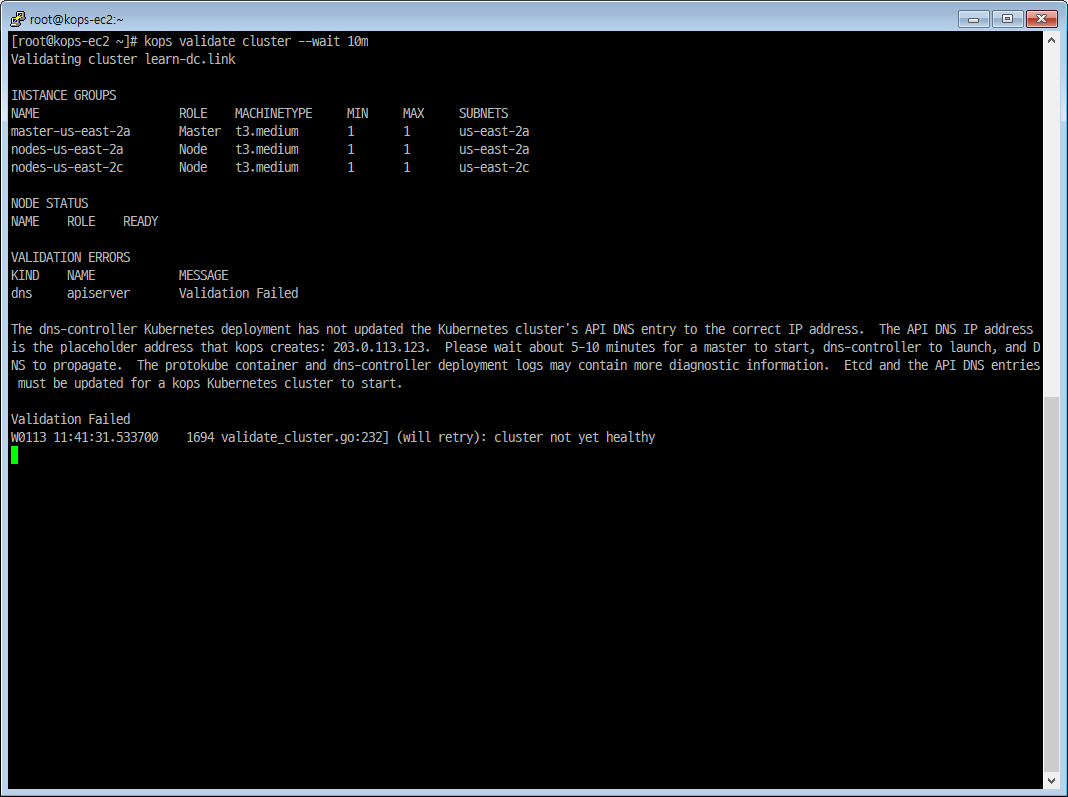
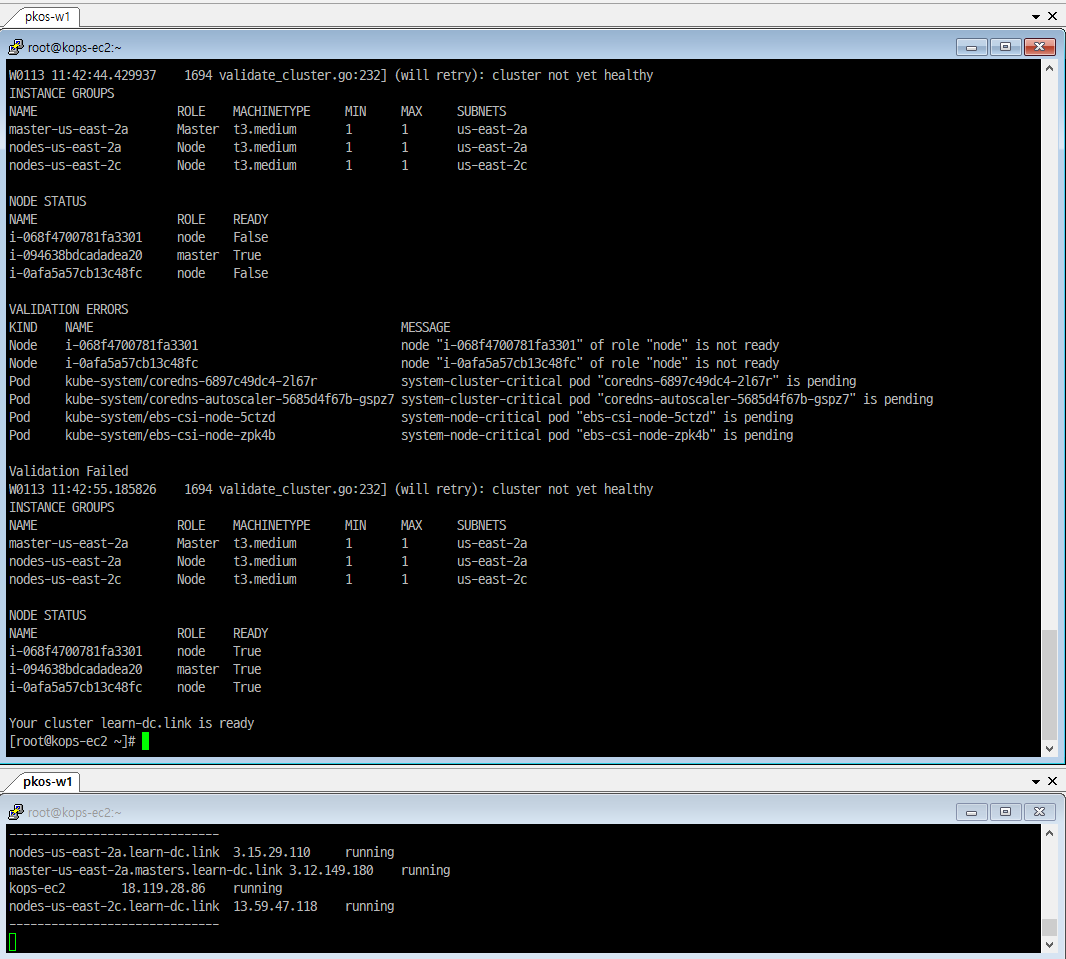
- Route53 에서 A 레코드 확인
kOps 설치 확인
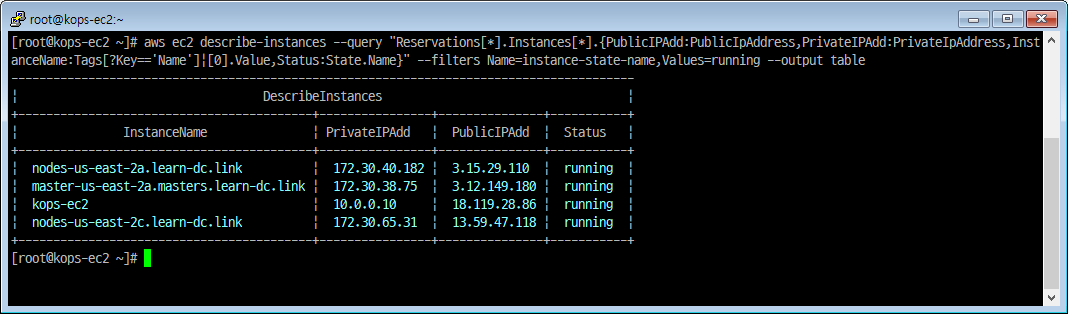
노드 IP 확인
|
|
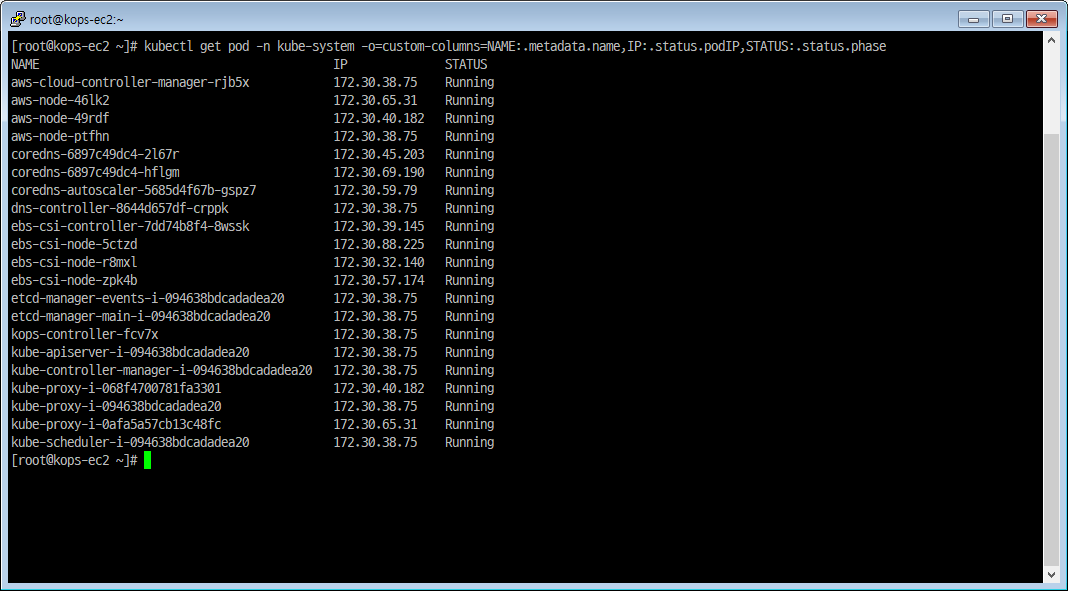
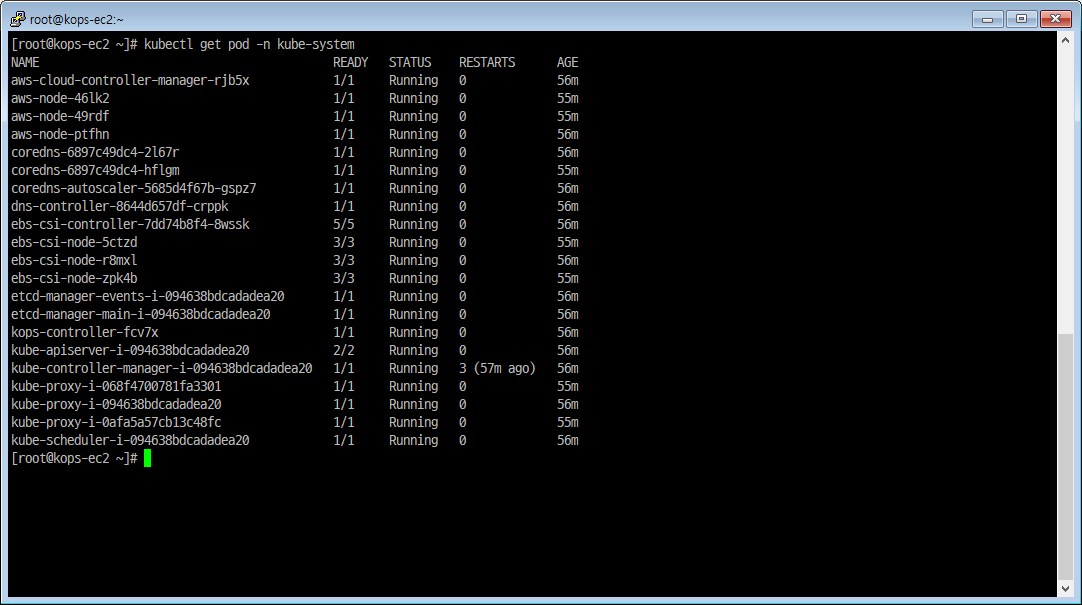
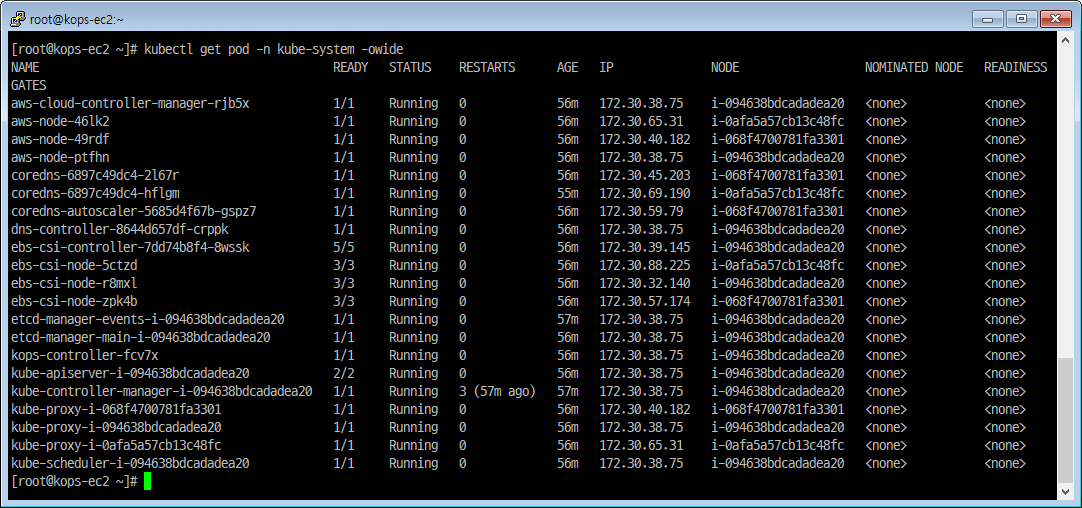
파드 IP 확인
|
|
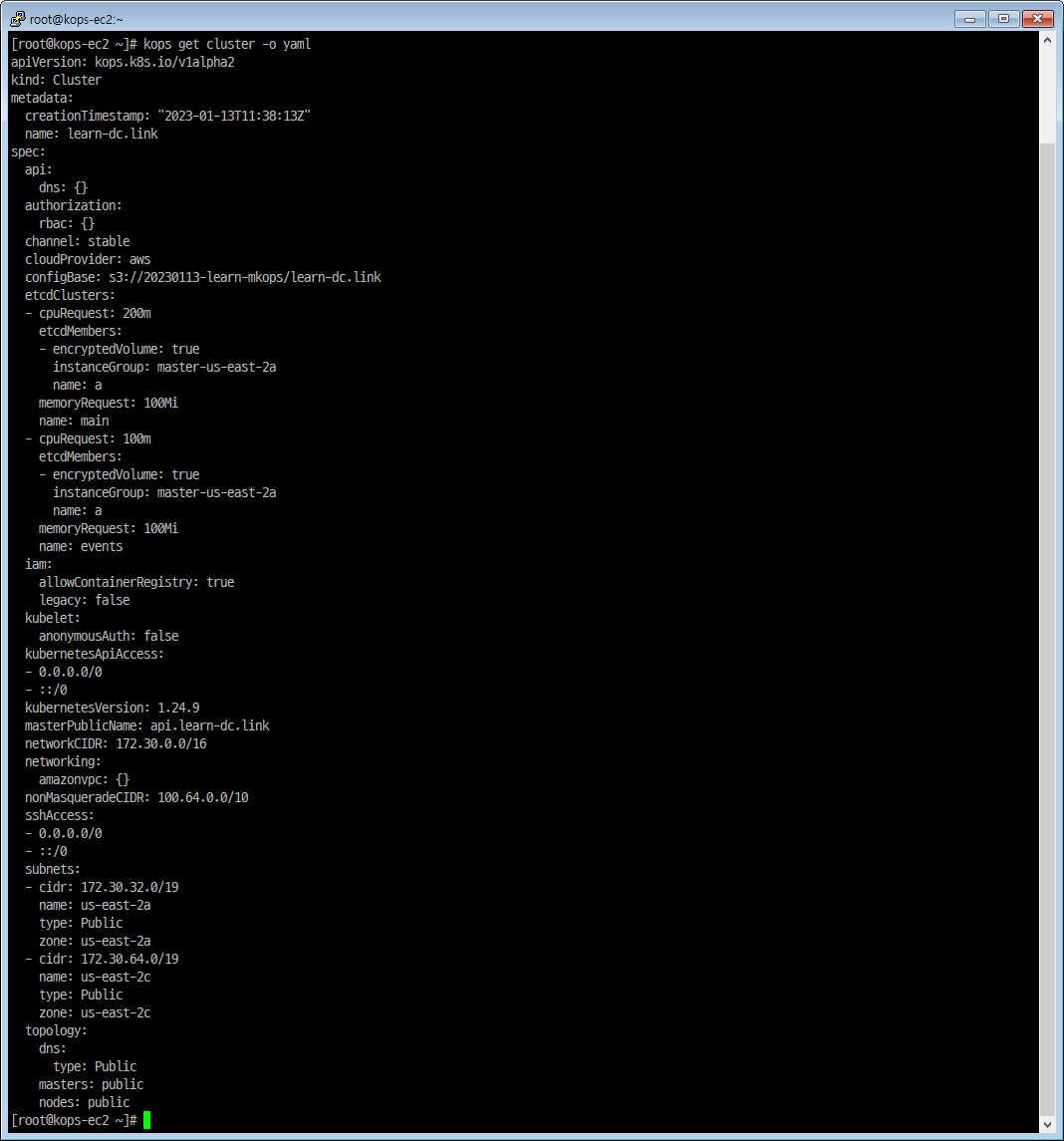
kops 클러스터 정보 확인
|
|
|
|
|
|
인스턴스 그룹 정보 확인
|
|
|
|
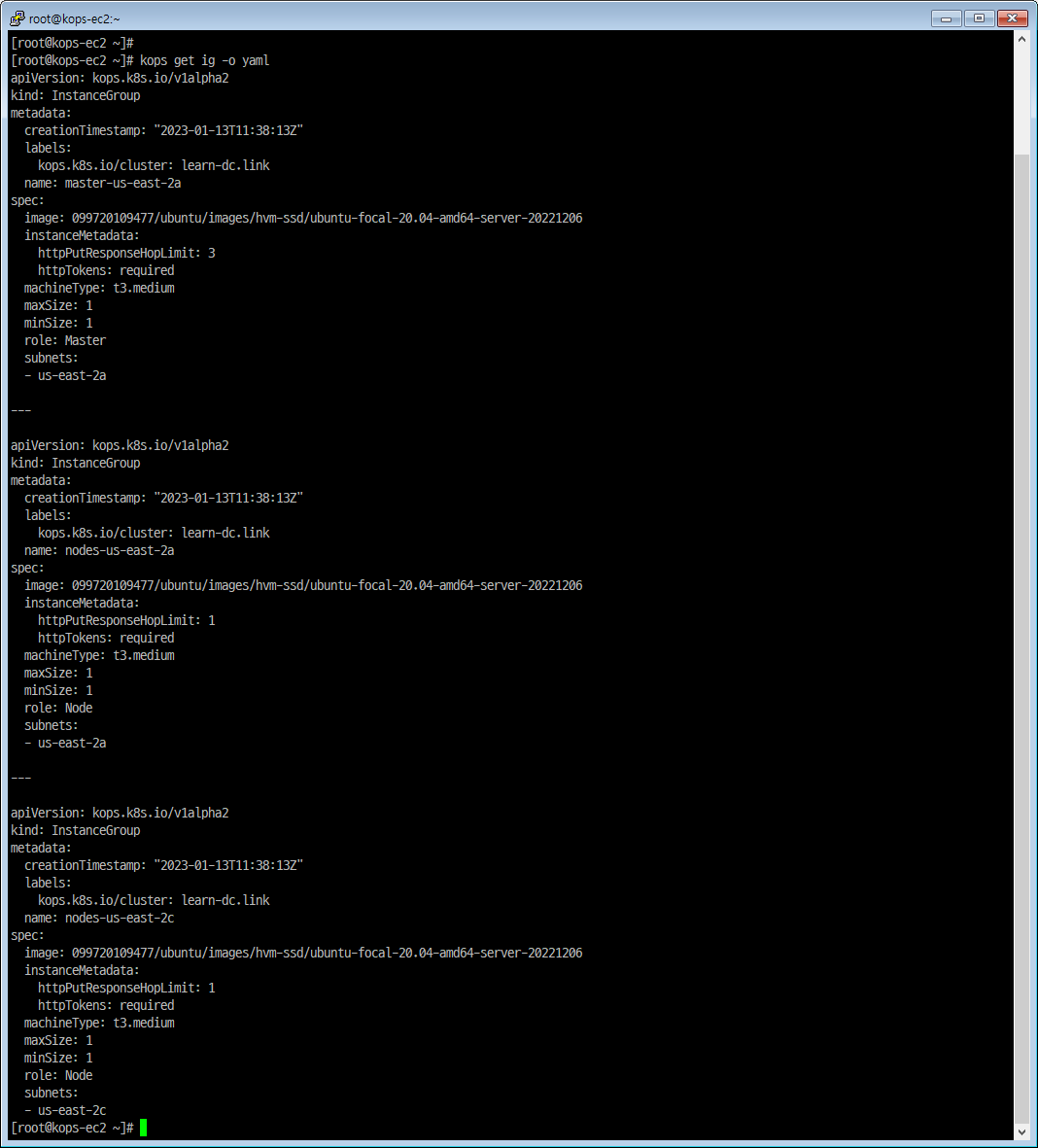
|
|
인스턴스 정보 확인
|
|
자동 완성 및 alias 축약 설정
|
|
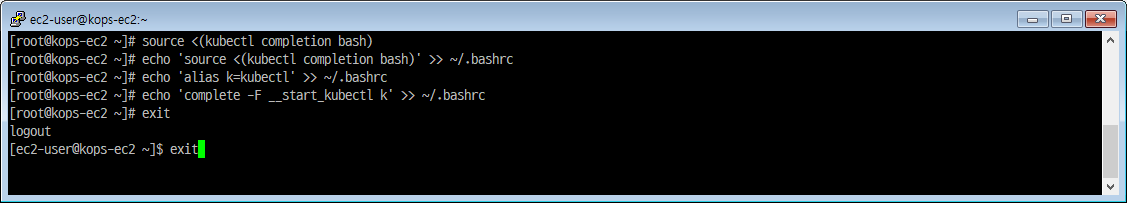
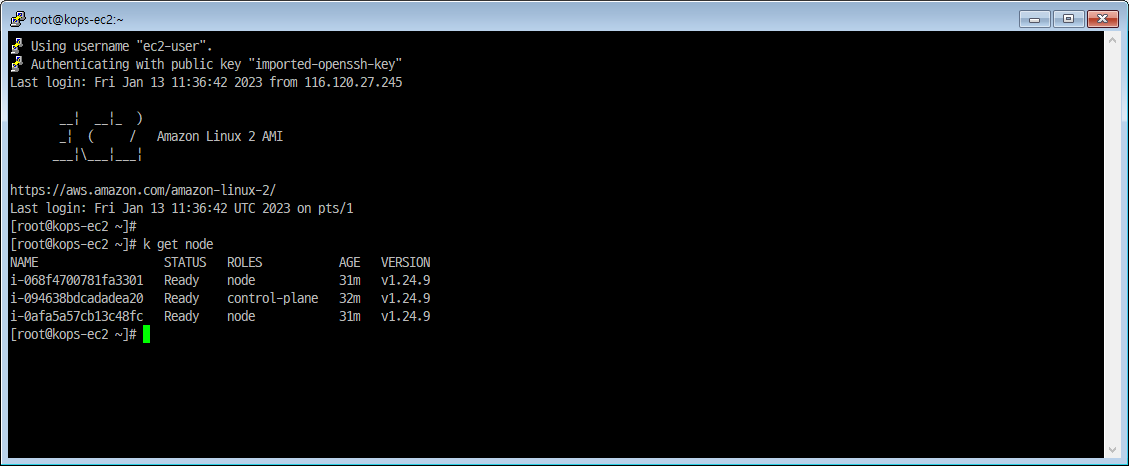
- ssh 재접속 후 명령어 확인
|
|
쿠버네티스 크루(krew) 설치
설치
|
|
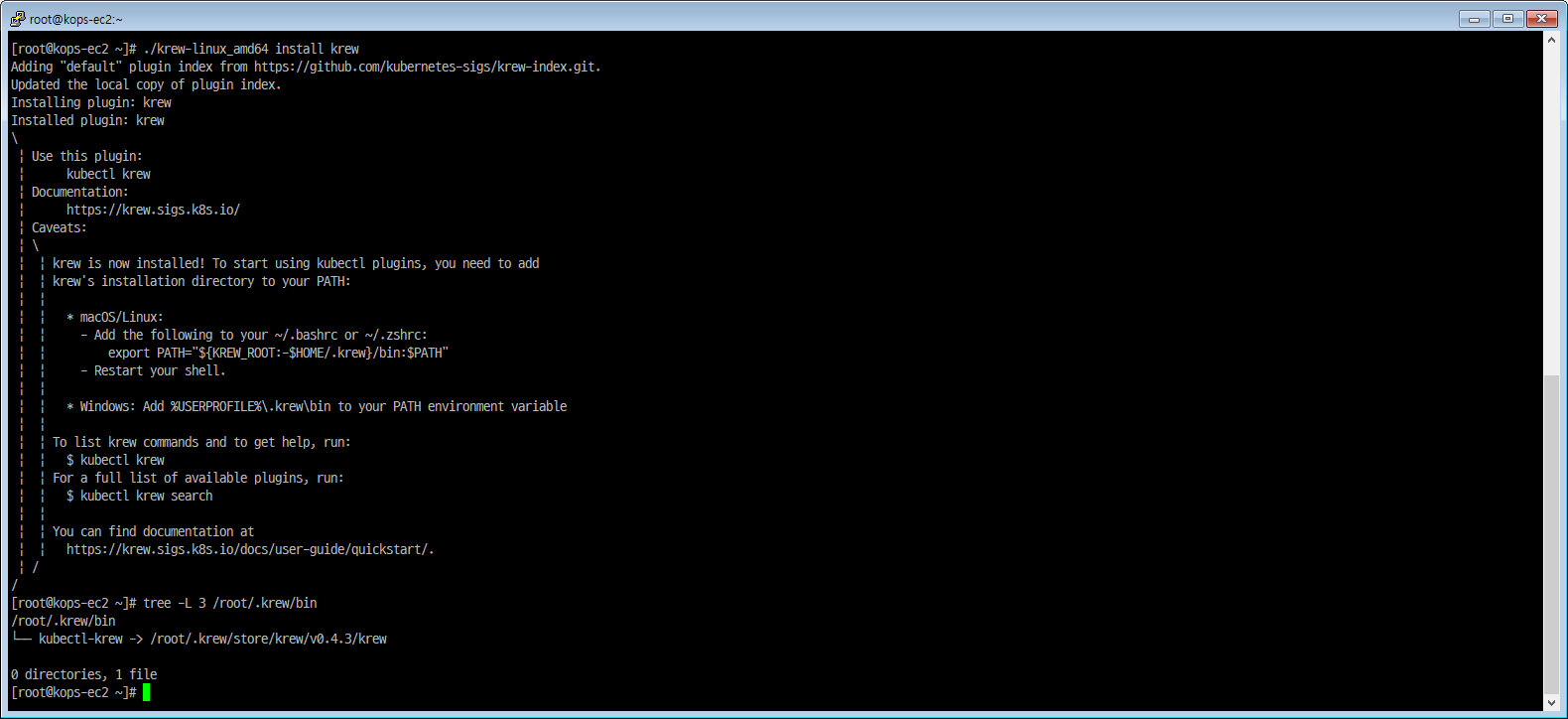
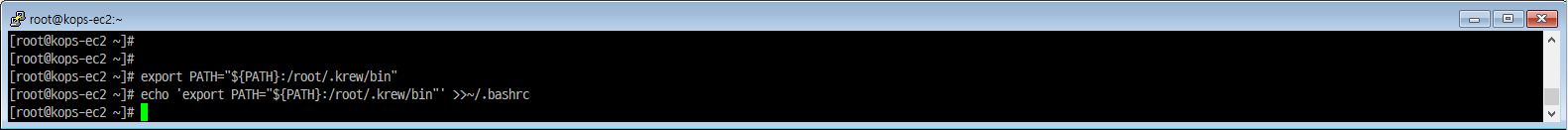
PATH 추가
|
|
krew 확인
|
|
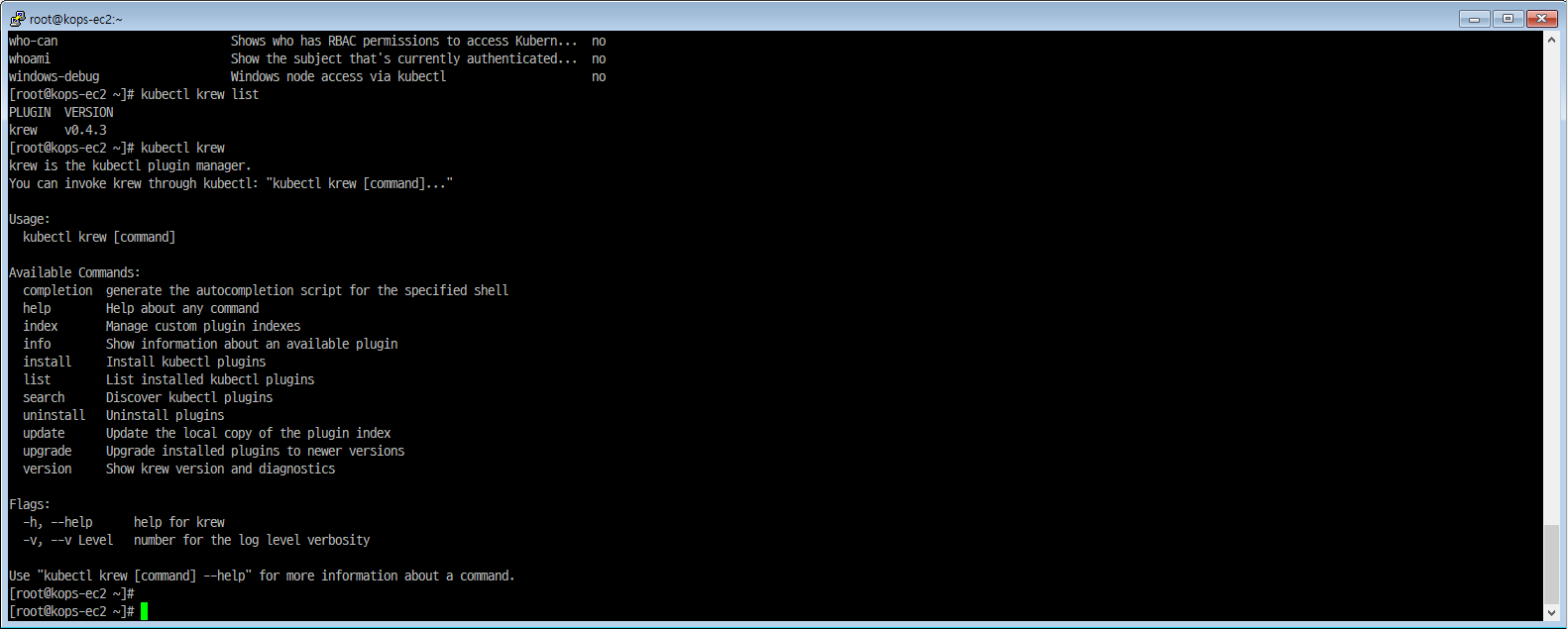
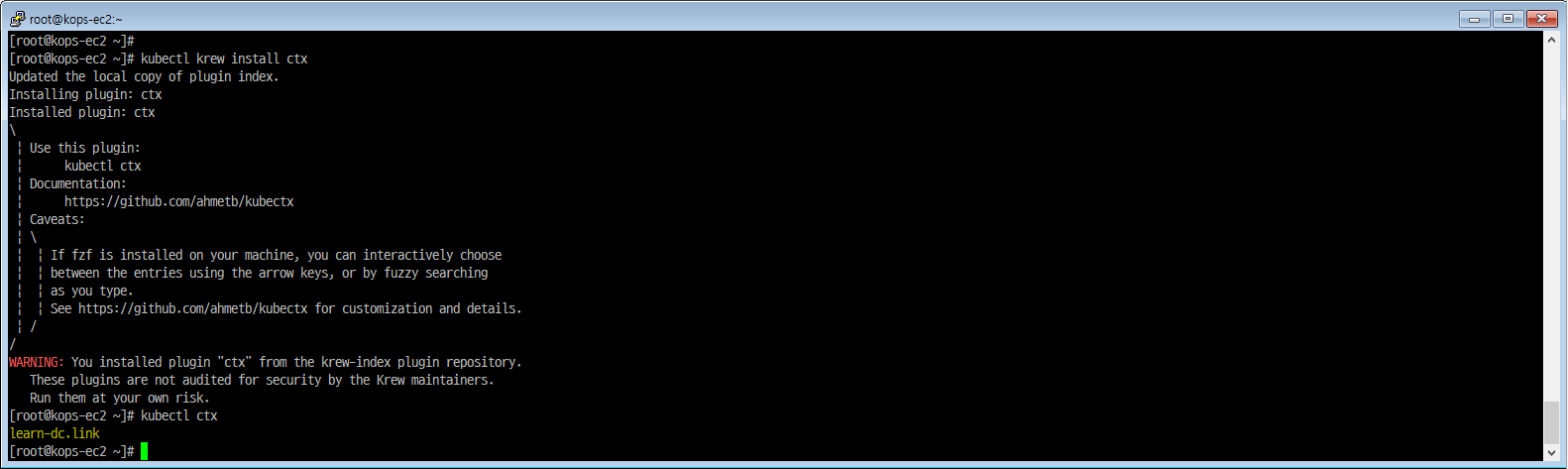
krew로 kube-* 플러그인 설치
- kube-ctx : 쿠버네티스 컨텍스트 사용
|
|
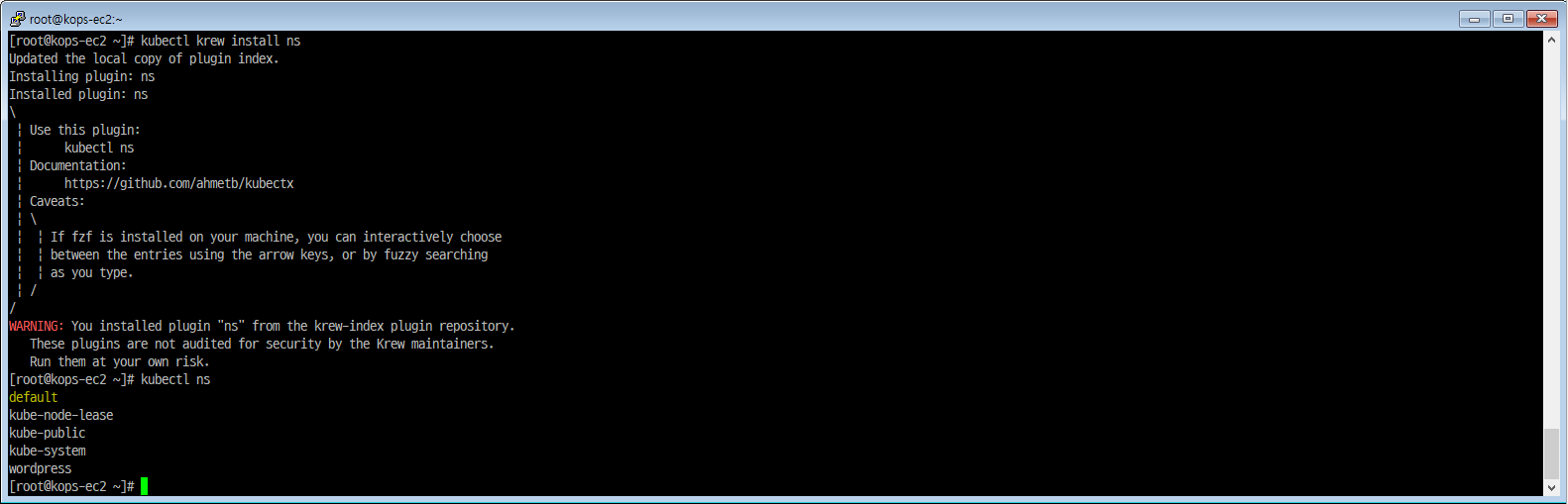
- kube-ns : 네임스페이스(단일 클러스터 내에서 가상 클러스터) 사용
|
|
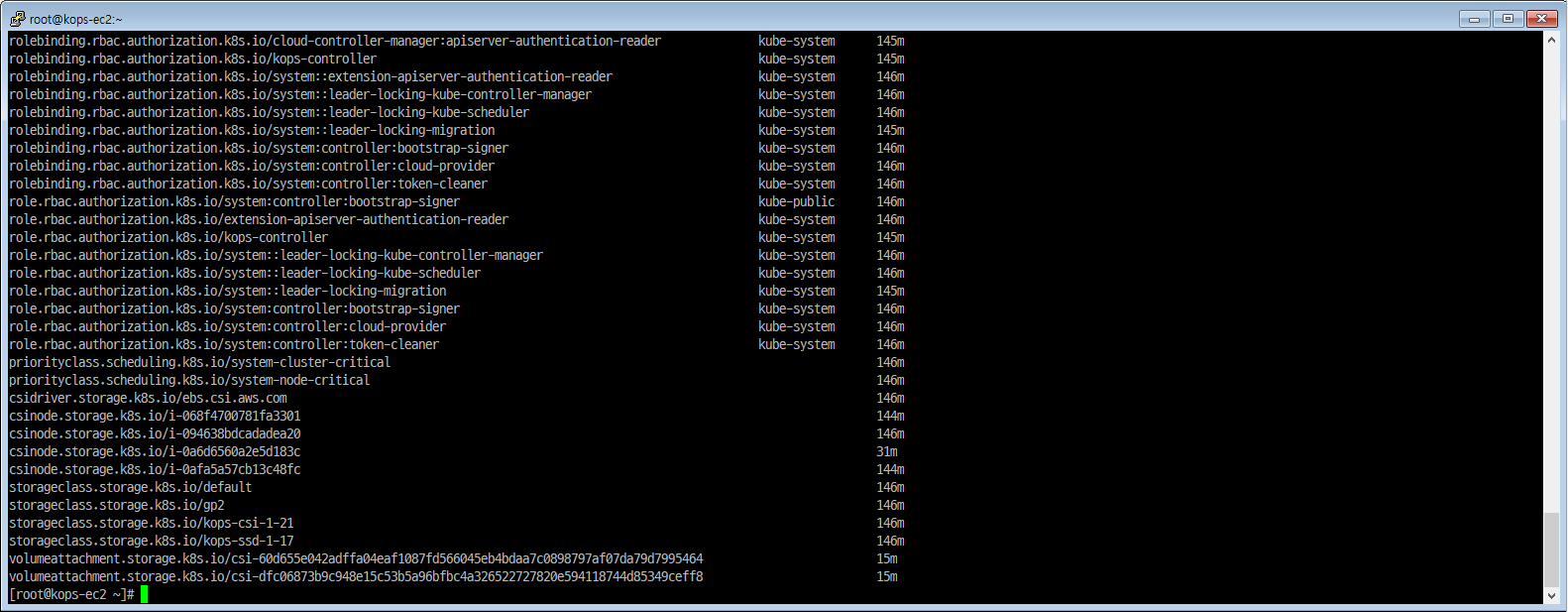
- kube-get-all :
|
|
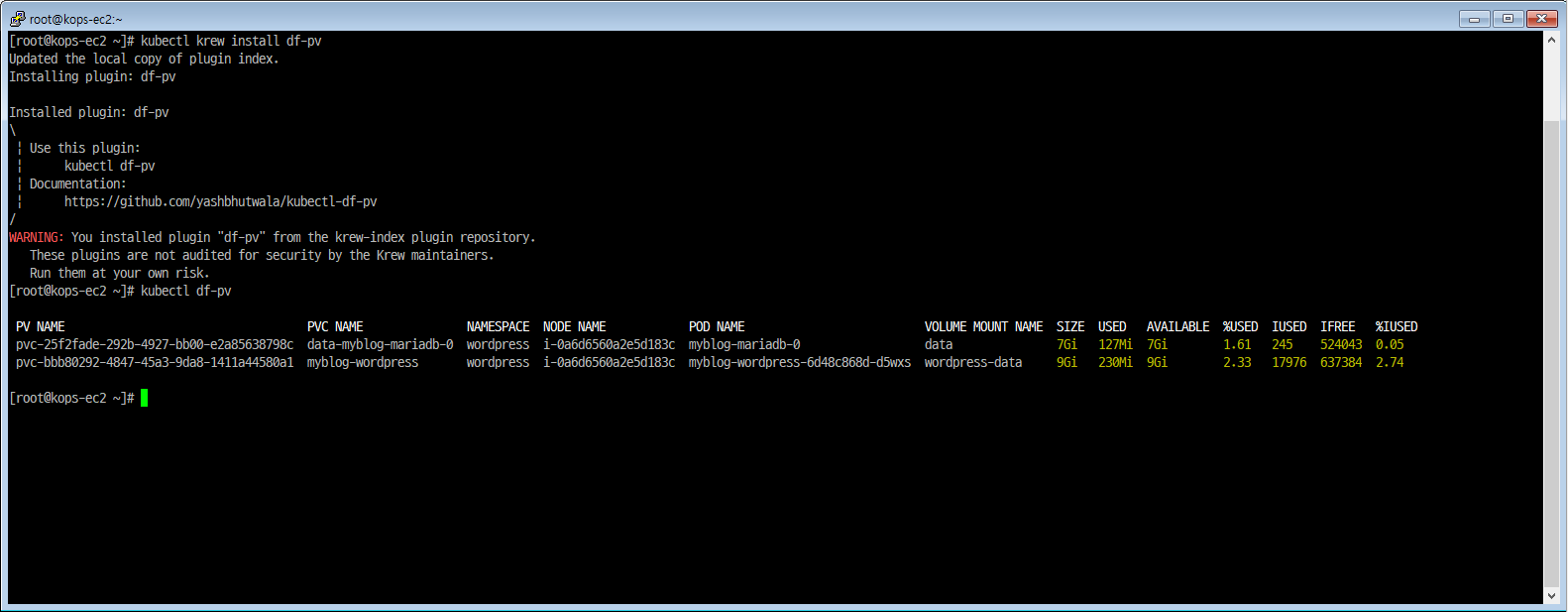
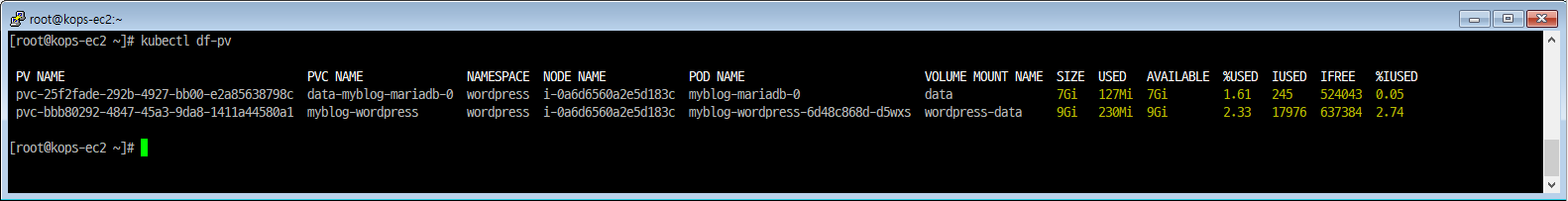
- kube-df-pv :
|
|
클러스터 정보 확인
|
|
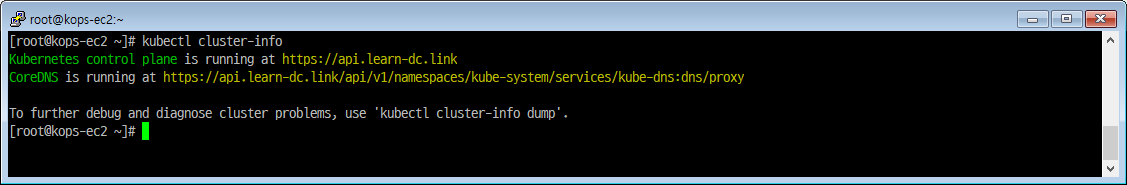
|
|
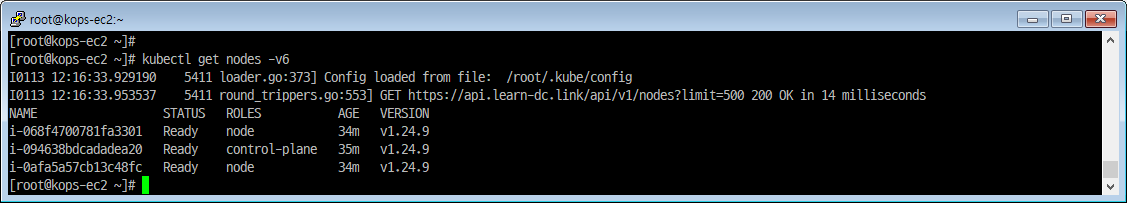
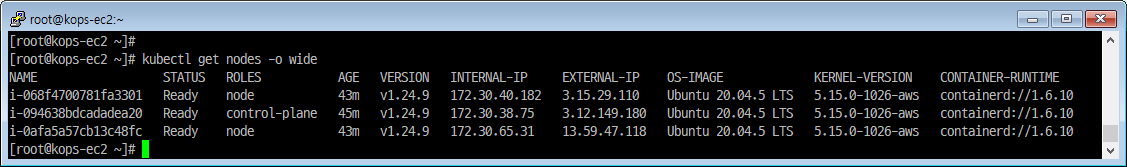
노드 정보 확인
-
Config loaded from file: /root/.kube/config이게 무엇인지?
|
|
CRI(Container Runtime Interface) 컨테이너 런타임
- CRI는 클러스터 컴포넌트를 다시 컴파일하지 않아도 Kubelet이 다양한 컨테이너 런타임을 사용할 수 있도록 하는 플러그인 인터페이스
|
|
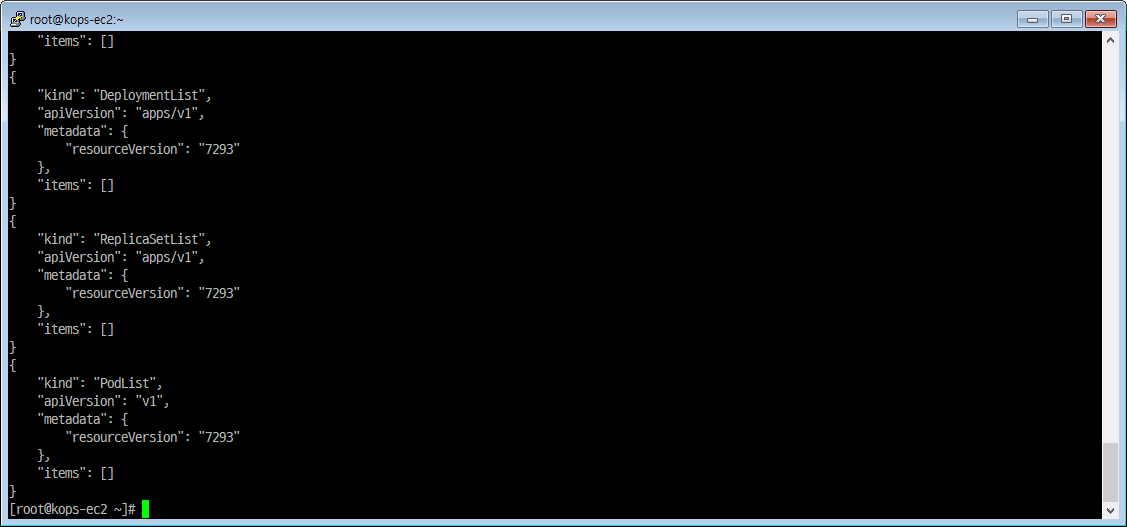
배포 완료 후 정보 확인
|
|
|
|
|
|
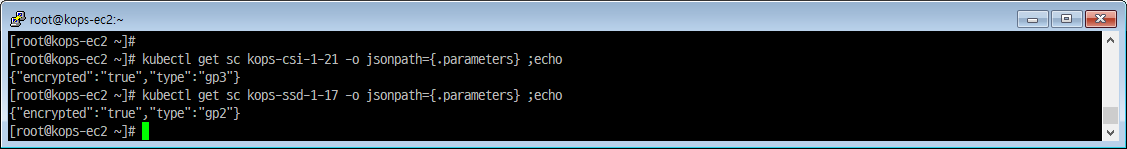
volume(sc)
- kubectl get sc == k get sc
- alias 축약 설정을 했기에
kubectl을k로 입력 가능
- alias 축약 설정을 했기에
|
|
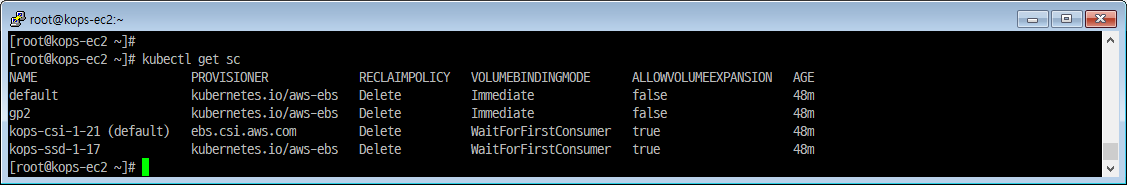
|
|
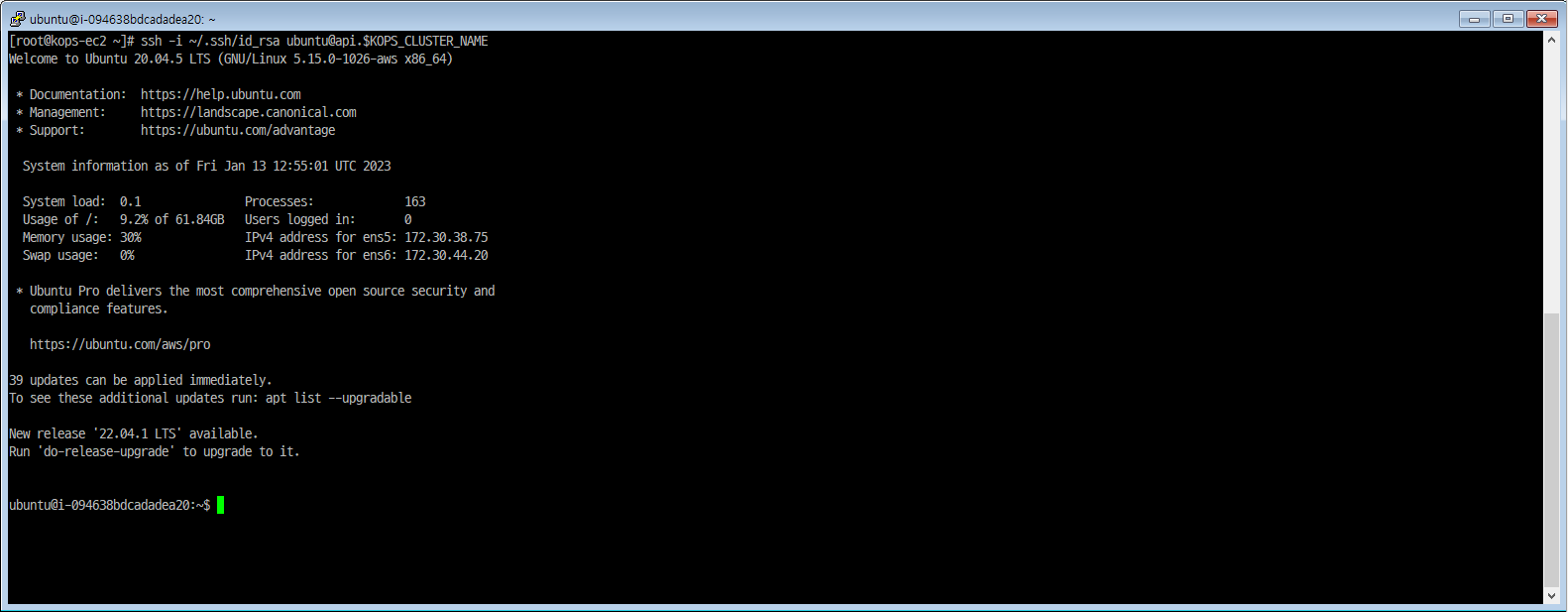
master node 원격 제어
[master node] aws vpc cni log
- master node 접근 방법
- ssh -i ~/.ssh/id_rsa ubuntu@api.$KOPS_CLUSTER_NAME
|
|
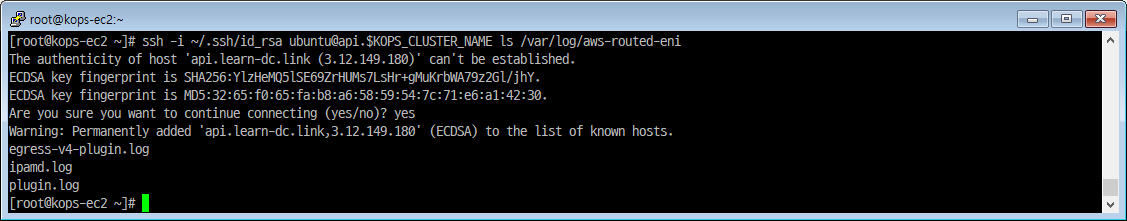
|
|
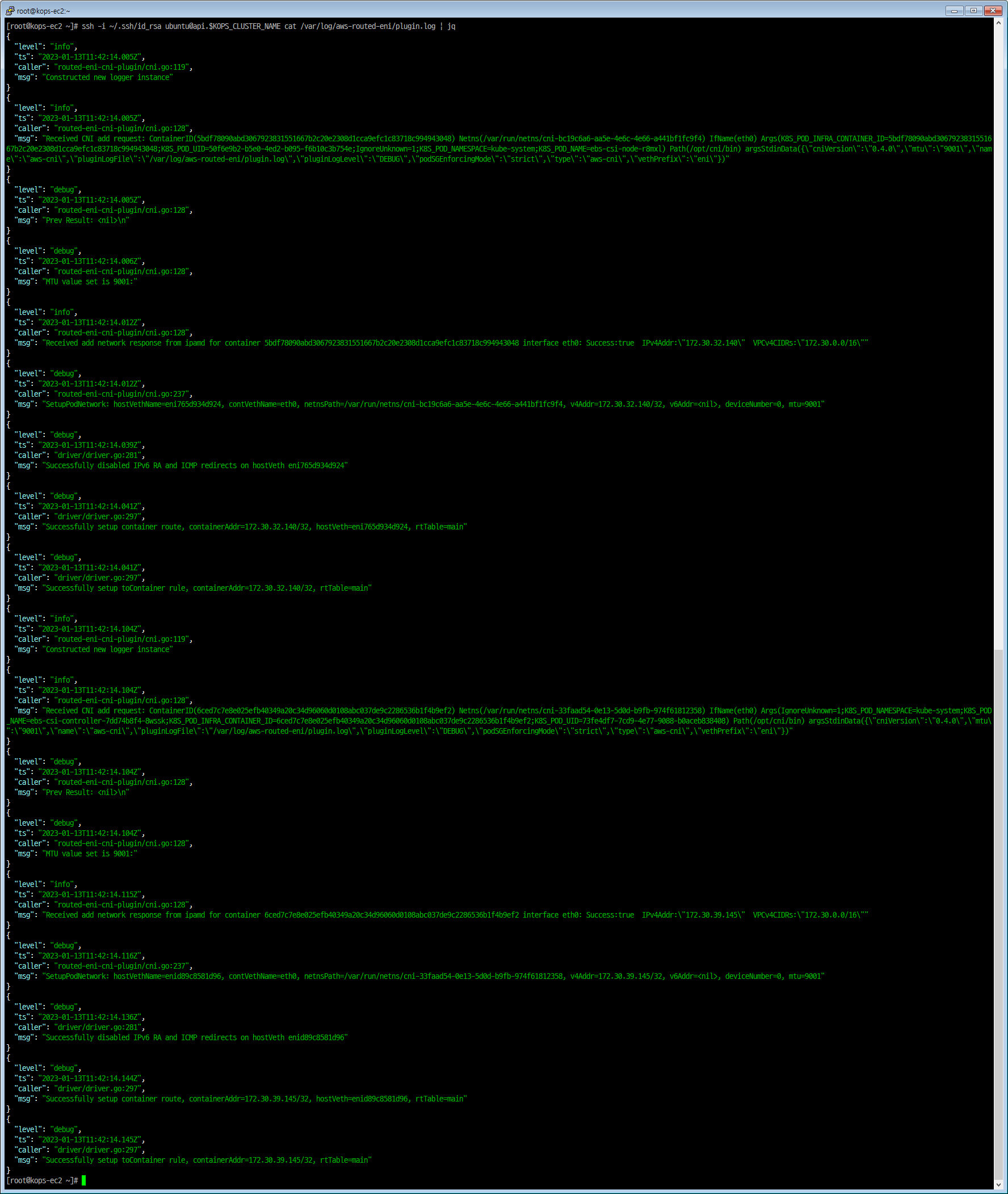
|
|
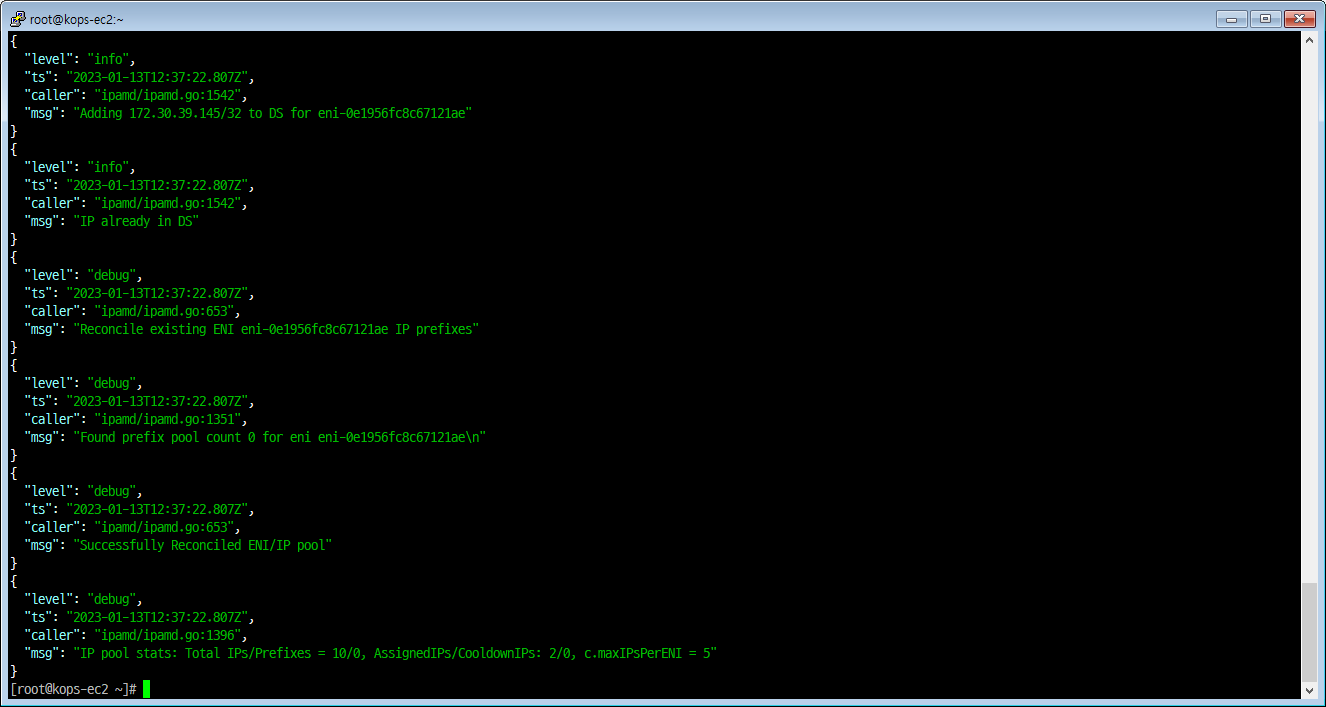
pod ip 확인
|
|
|
|
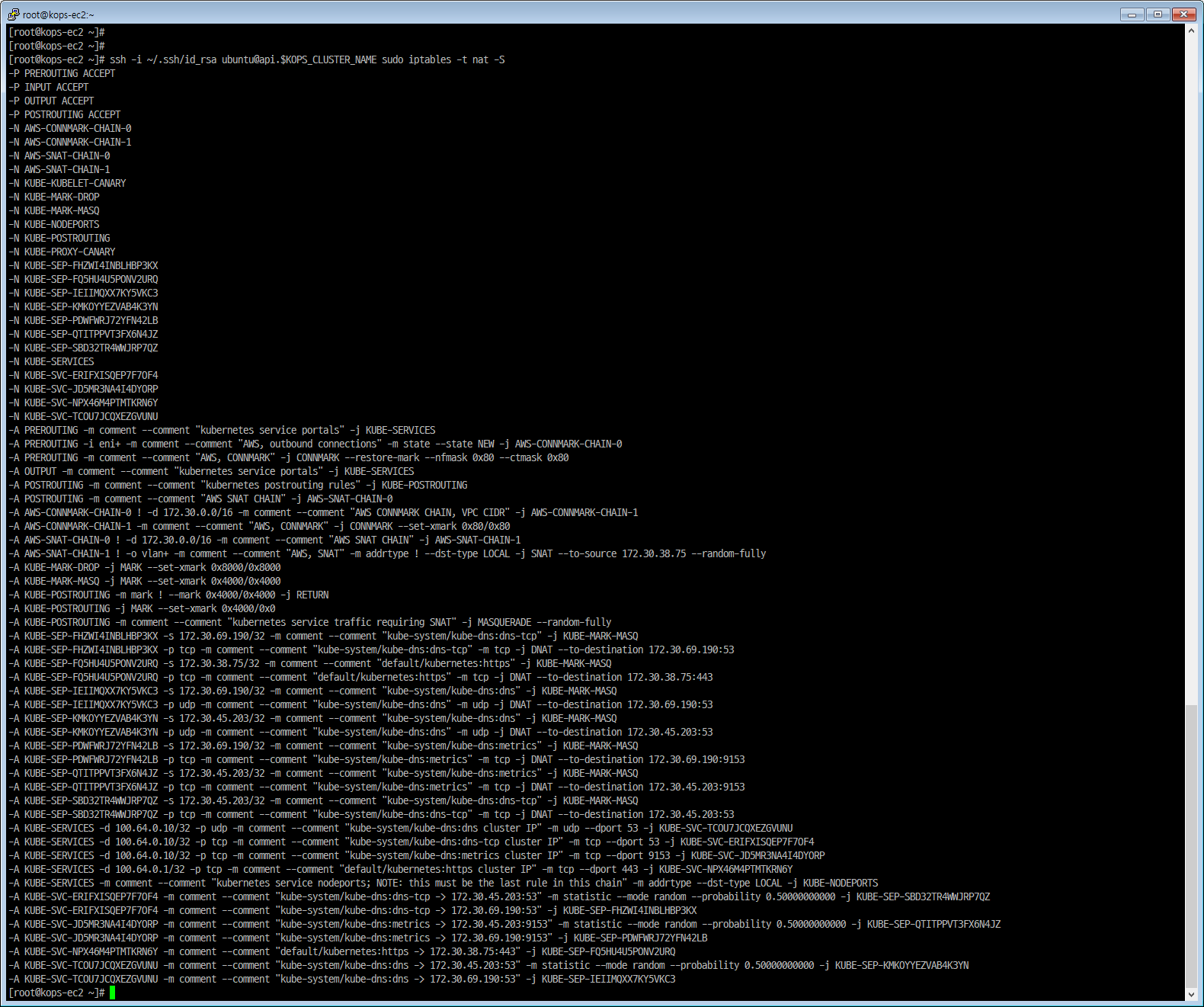
[master node] iptables rules
|
|
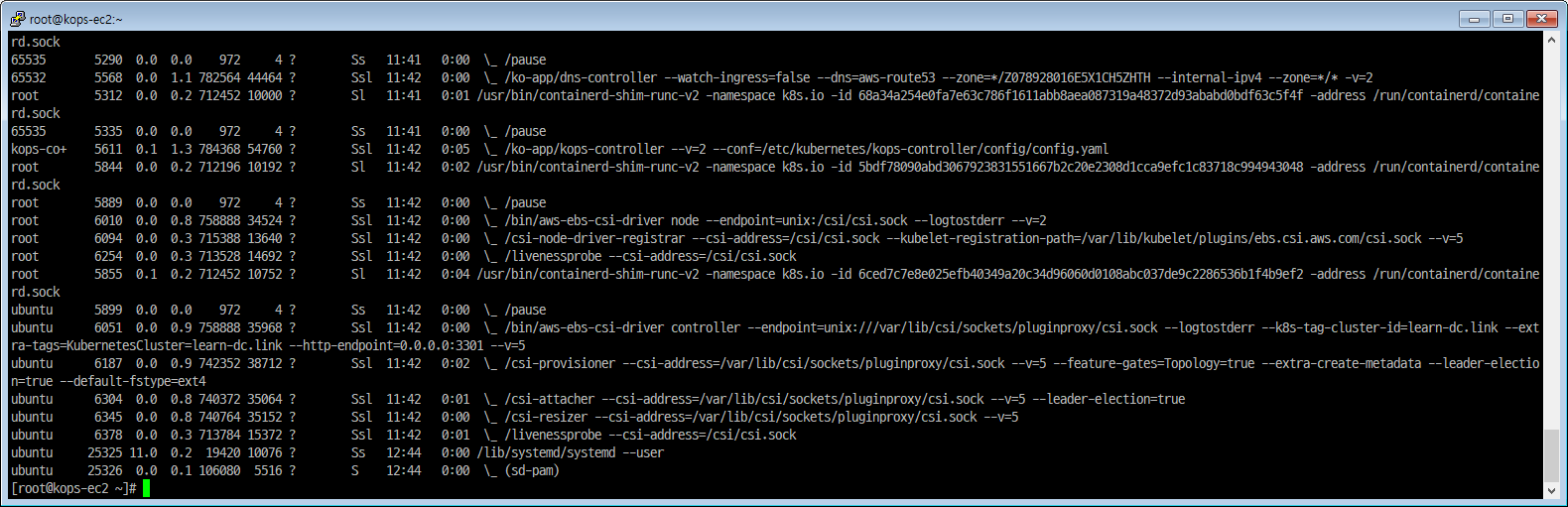
[master node] 컨테이너 정보 확인
|
|
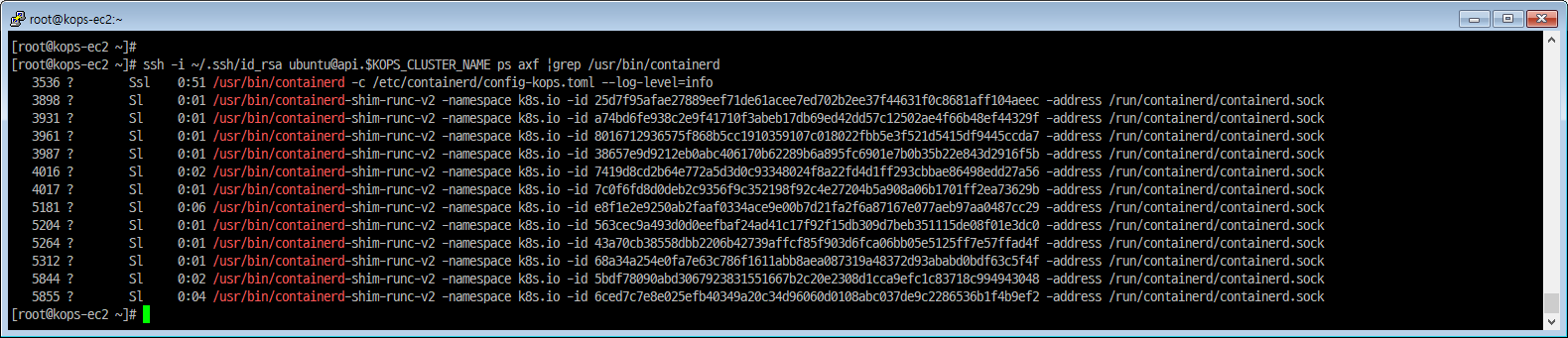
|
|
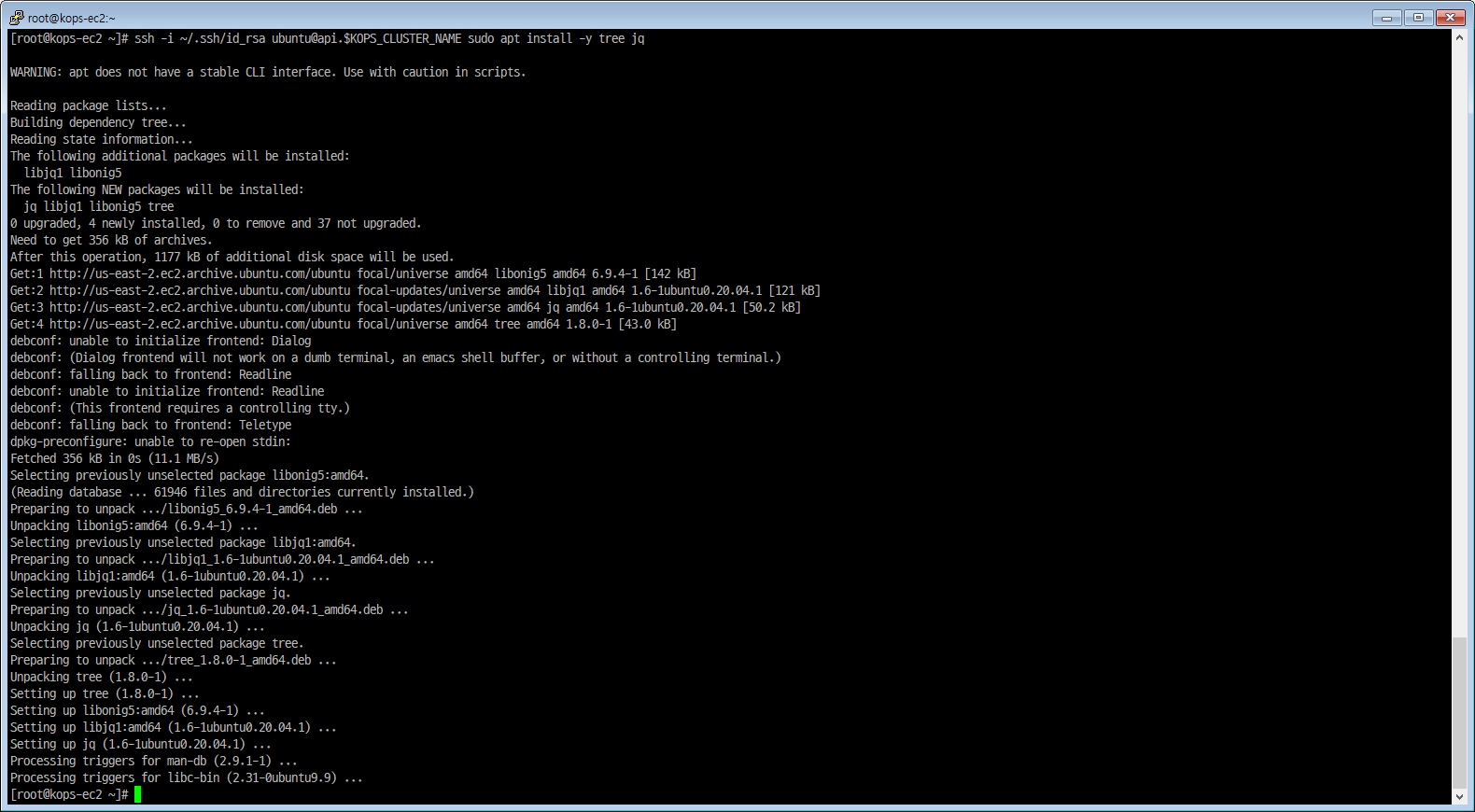
[master node] tree 툴 설치
|
|
[master node] Static 파드 정보 확인
- Static Pod는 API 서버 없이 특정 노드에 있는 kubelet 데몬에 의해 직접 관리
|
|
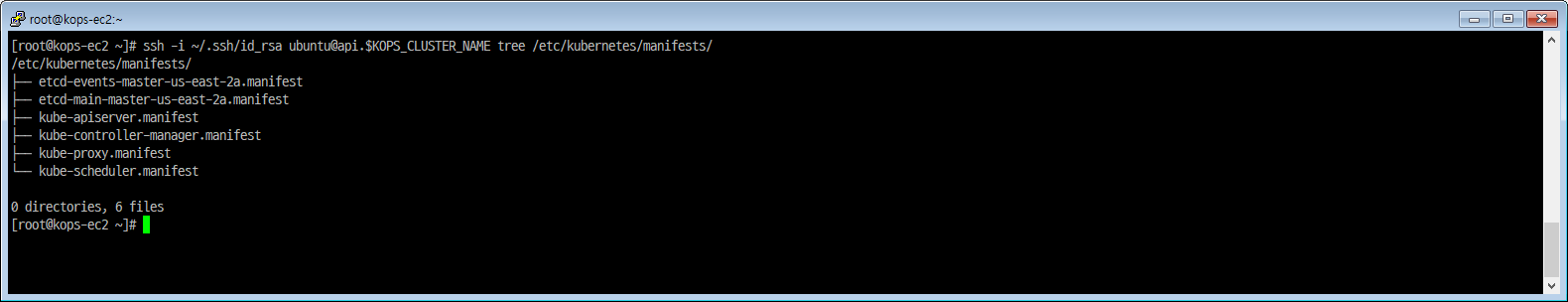
|
|
|
|
|
|
|
|
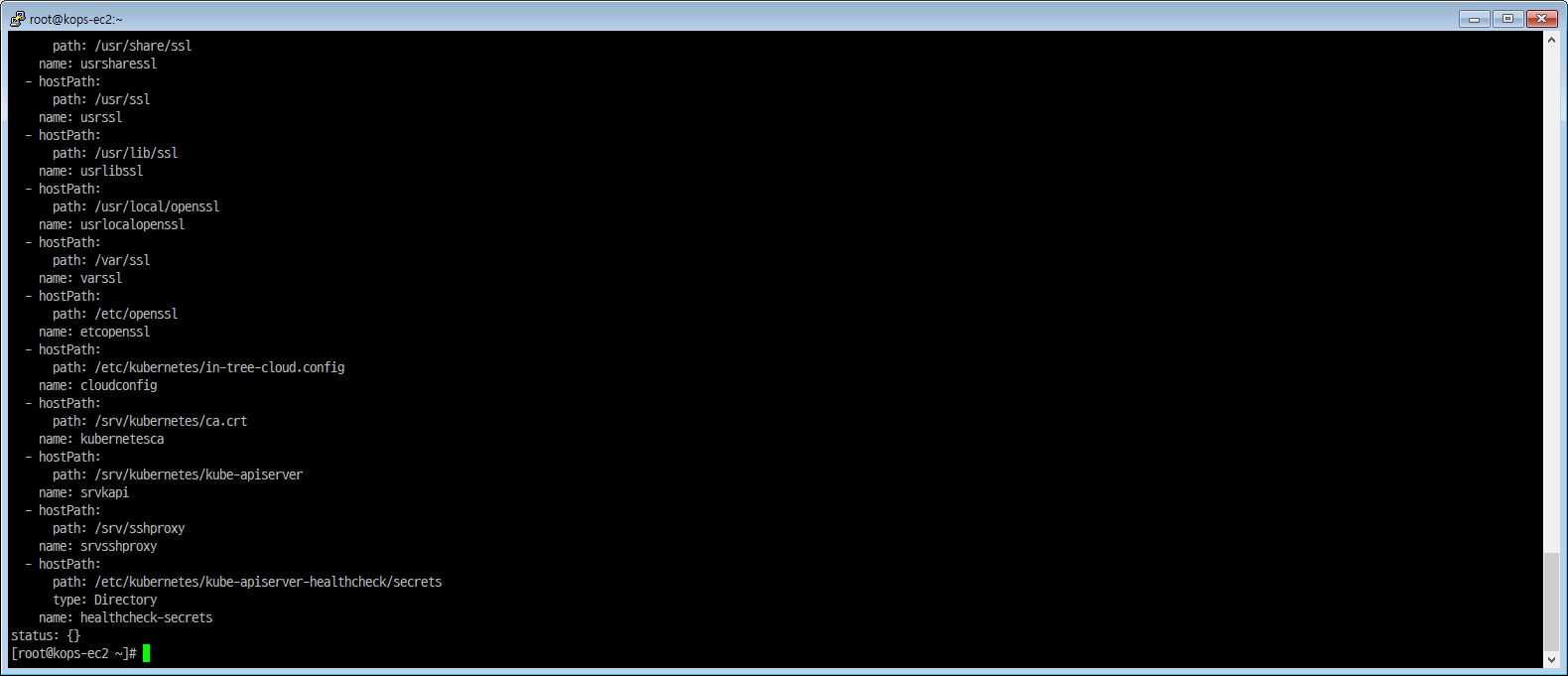
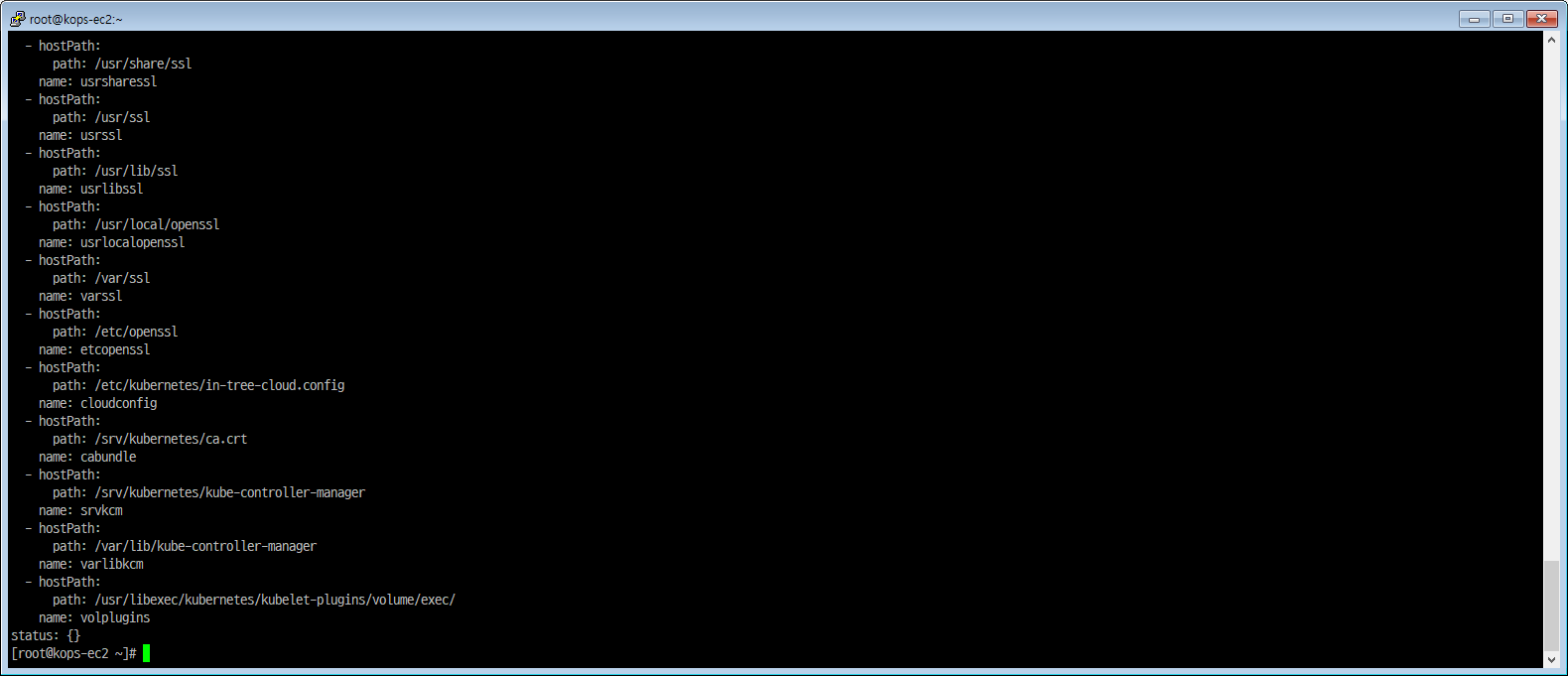
[master node] 볼륨/마운트 확인
- nvme1n1 과 nvme2n1 은 etcd-events, etcd-main 으로 사용
|
|
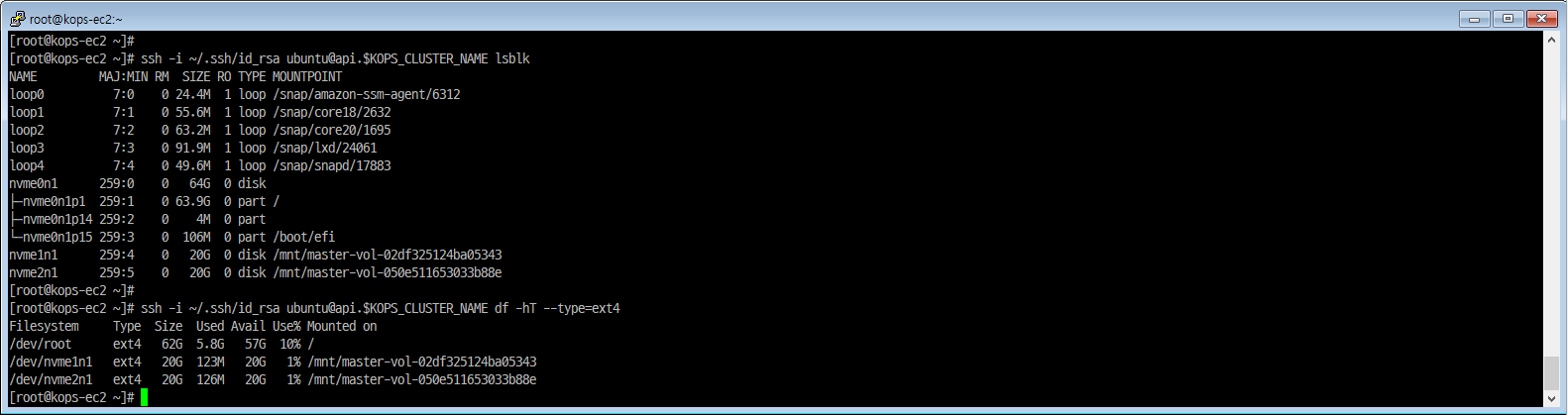
[master node] nvme1n1, nvme1n2 디렉터리 확인
|
|
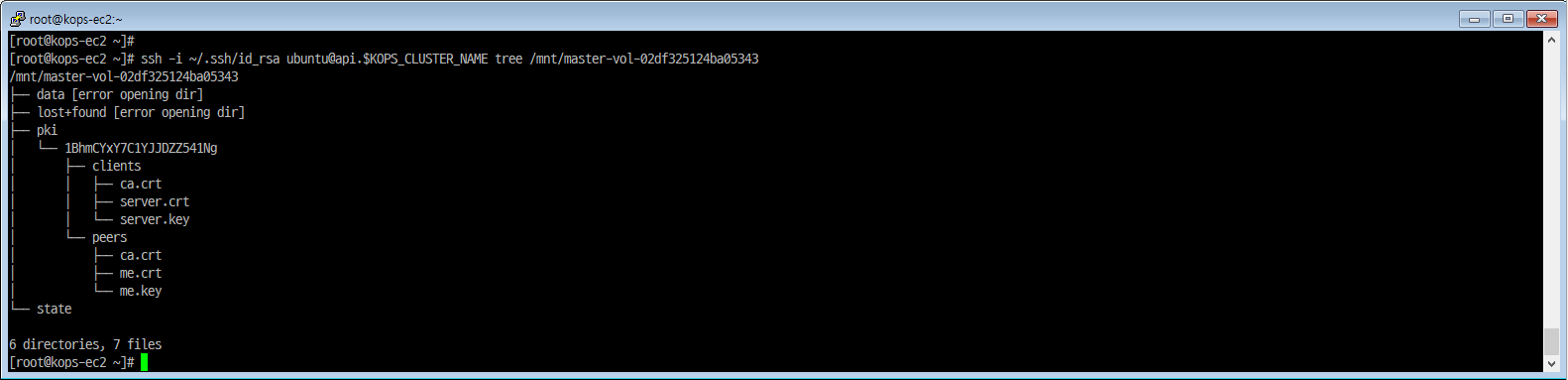
|
|
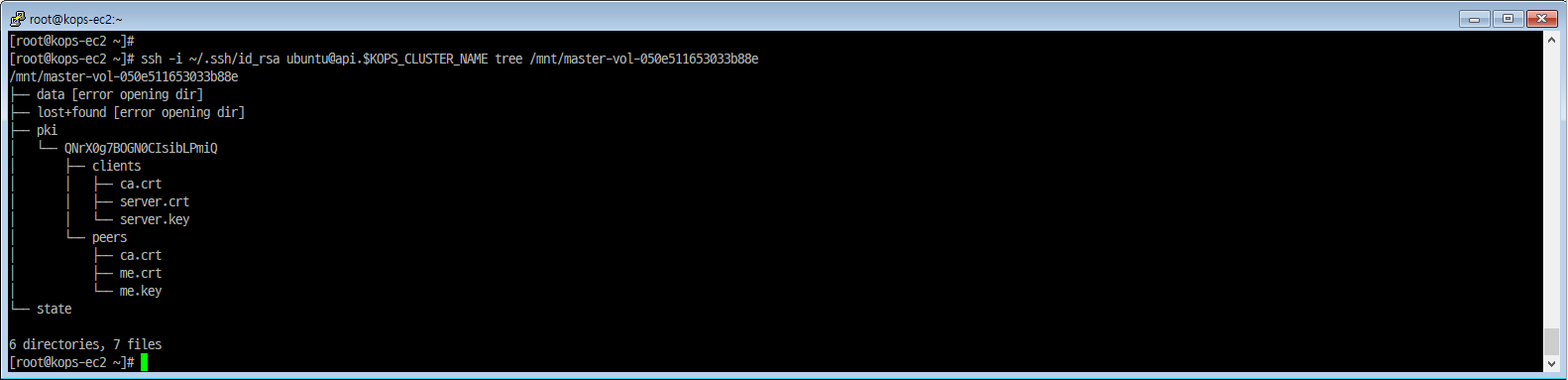
[master node] kubelet 상태 확인
|
|
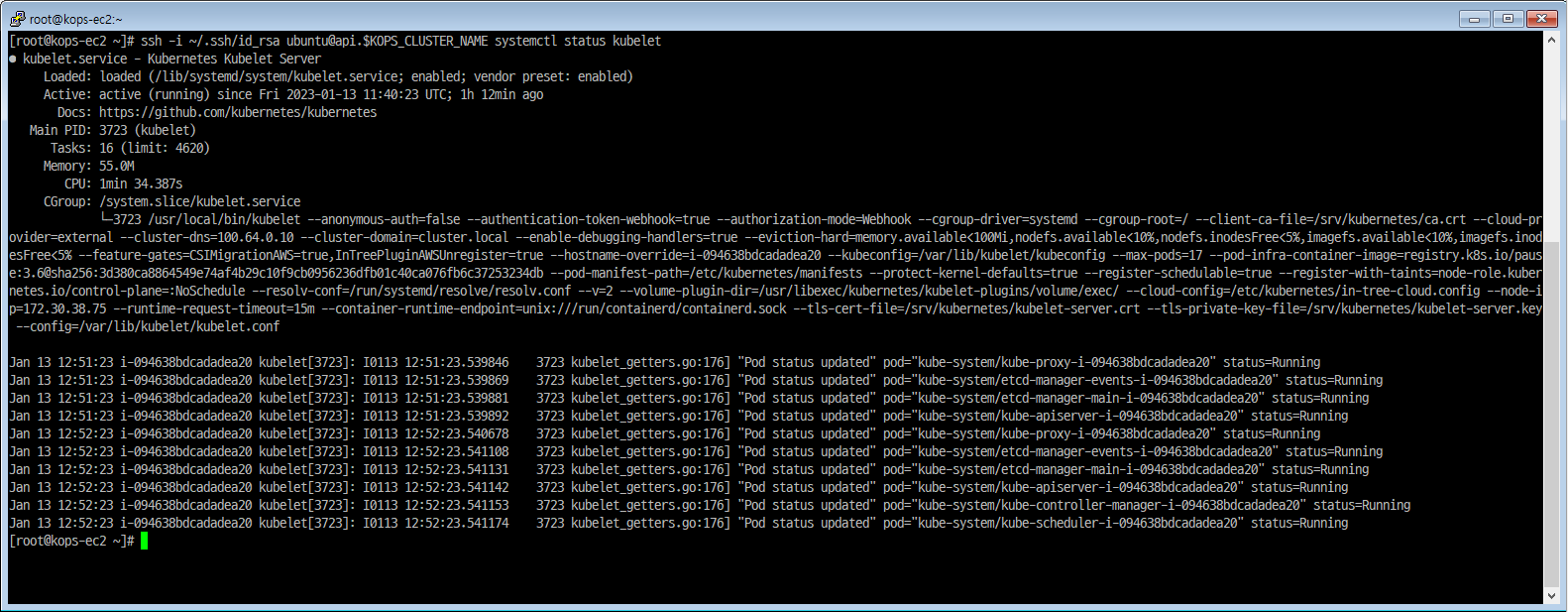
master node 접속
[master node] SSH 접속
|
|
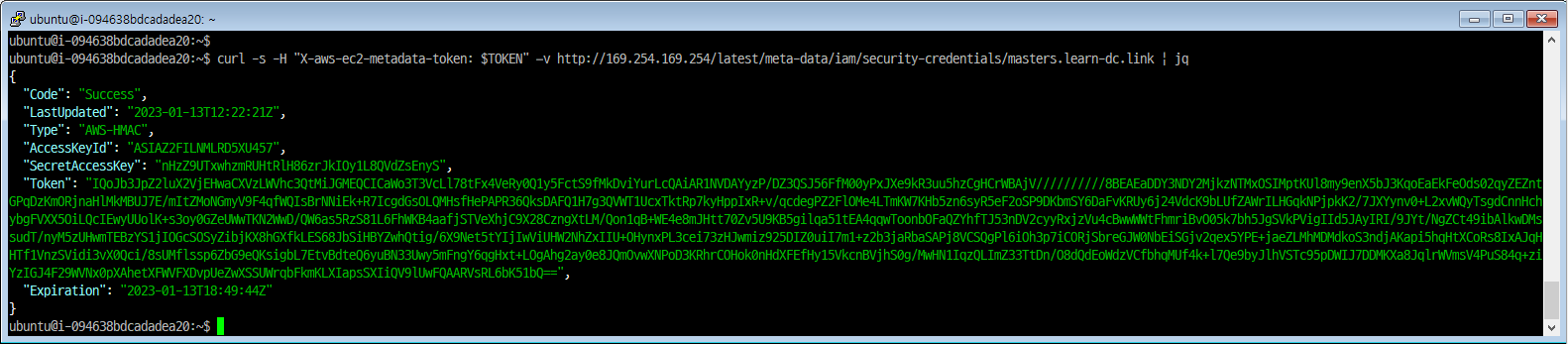
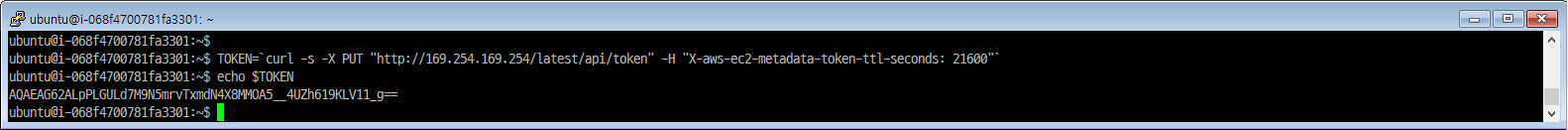
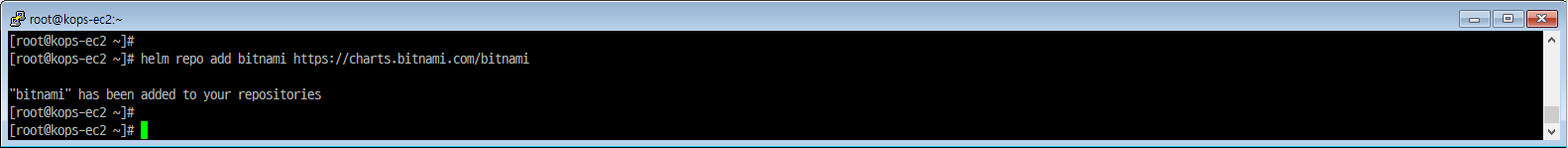
[master node] EC2 메타데이터 확인
|
|
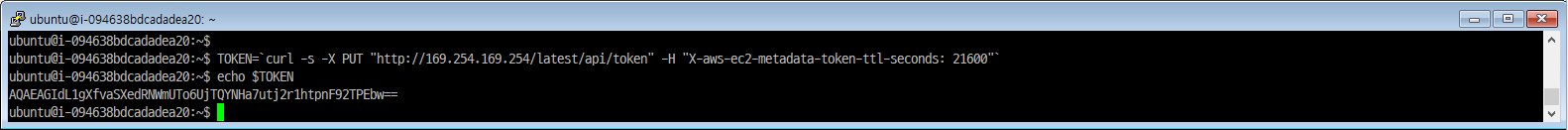
|
|
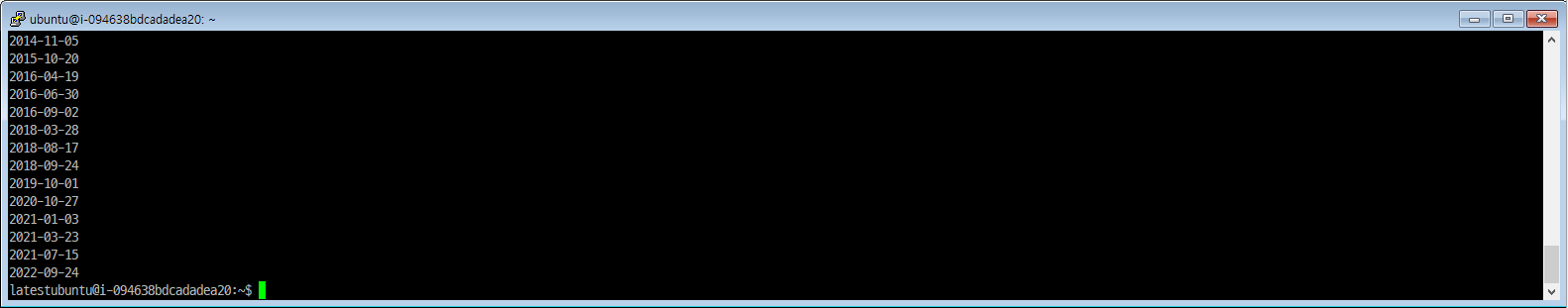
|
|
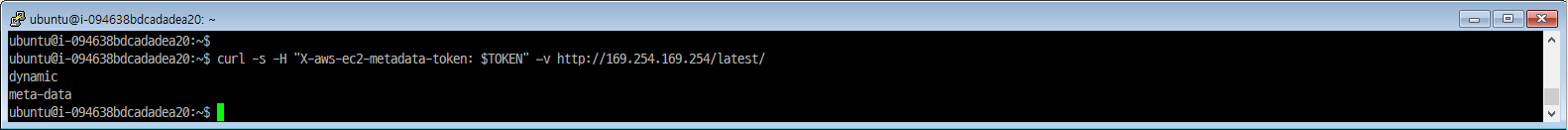
|
|
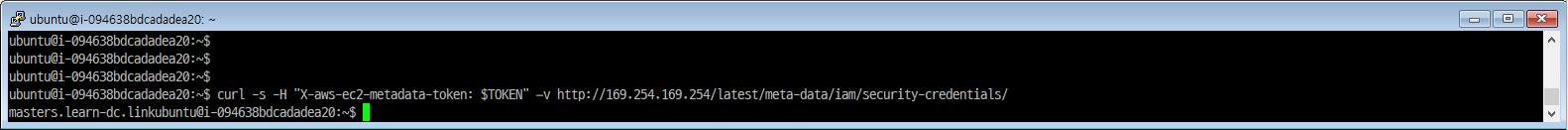
|
|
worker node 접속 확인
[worker node] Public IP 확인
|
|
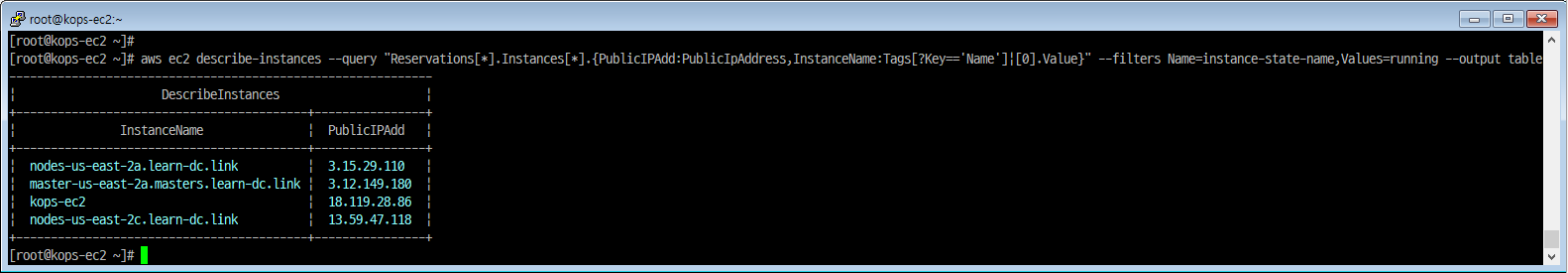
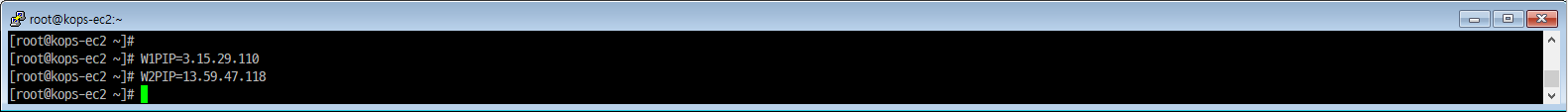
[worker node] Public IP 변수 지정
- W1PIP=<워커 노드 1 Public IP>
- W2PIP=<워커 노드 2 Public IP>
- W1PIP=3.35.50.183
- W2PIP=54.180.118.11
|
|
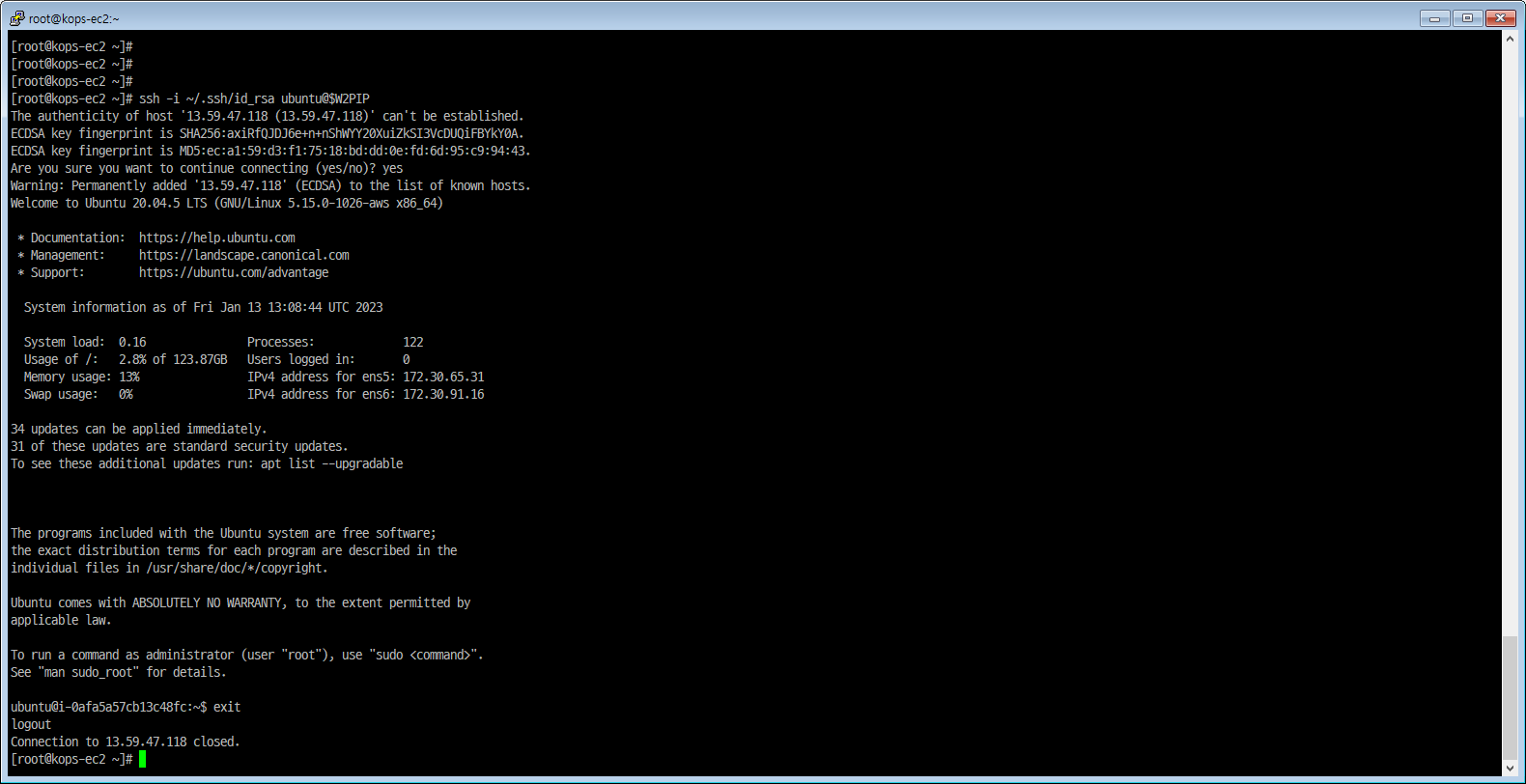
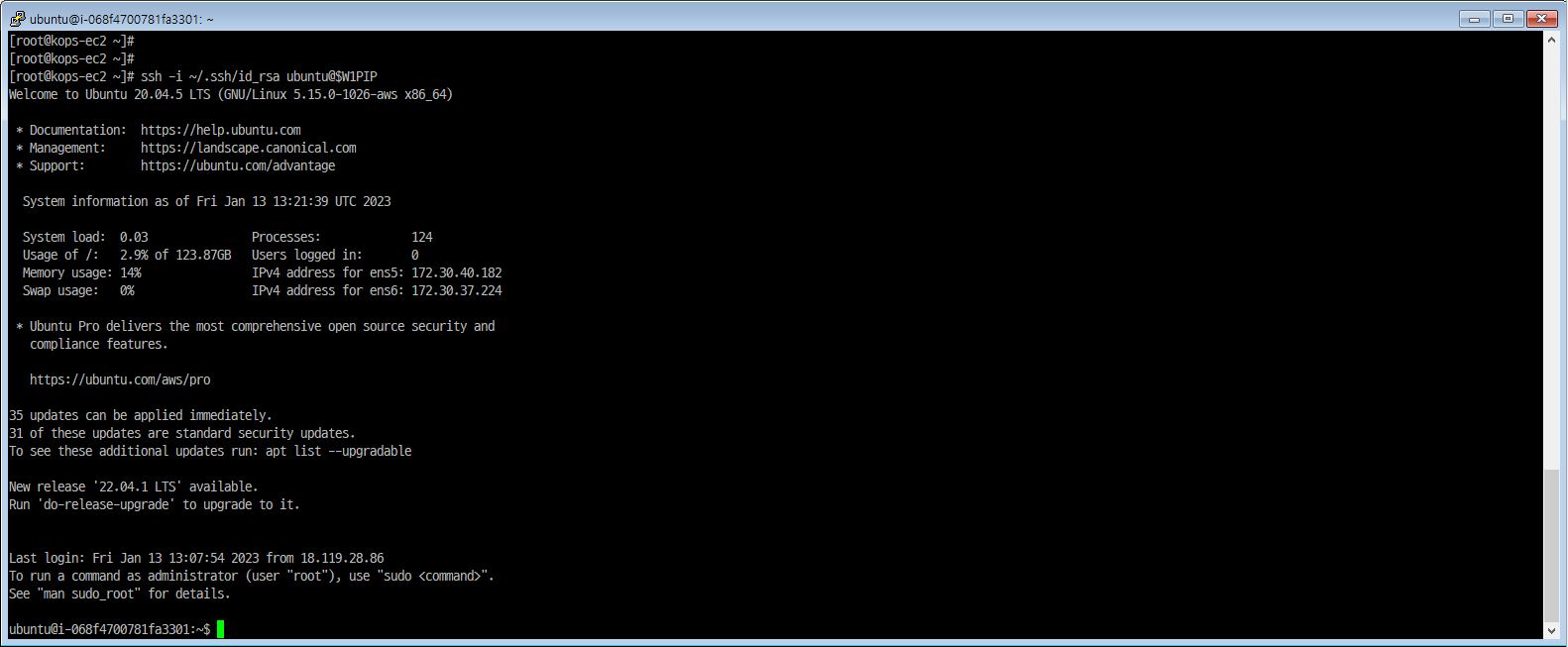
[worker node] SSH 접속
|
|
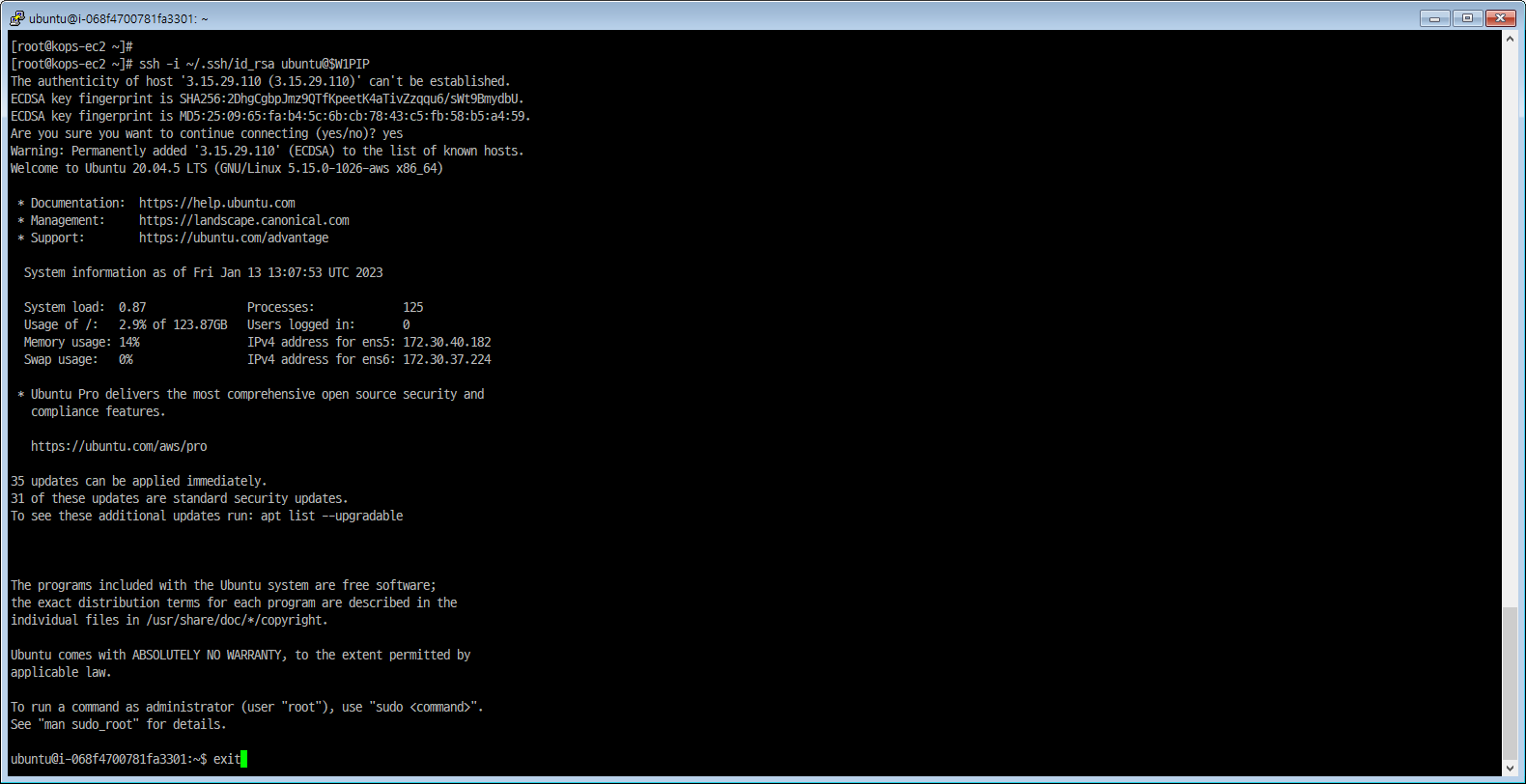
|
|
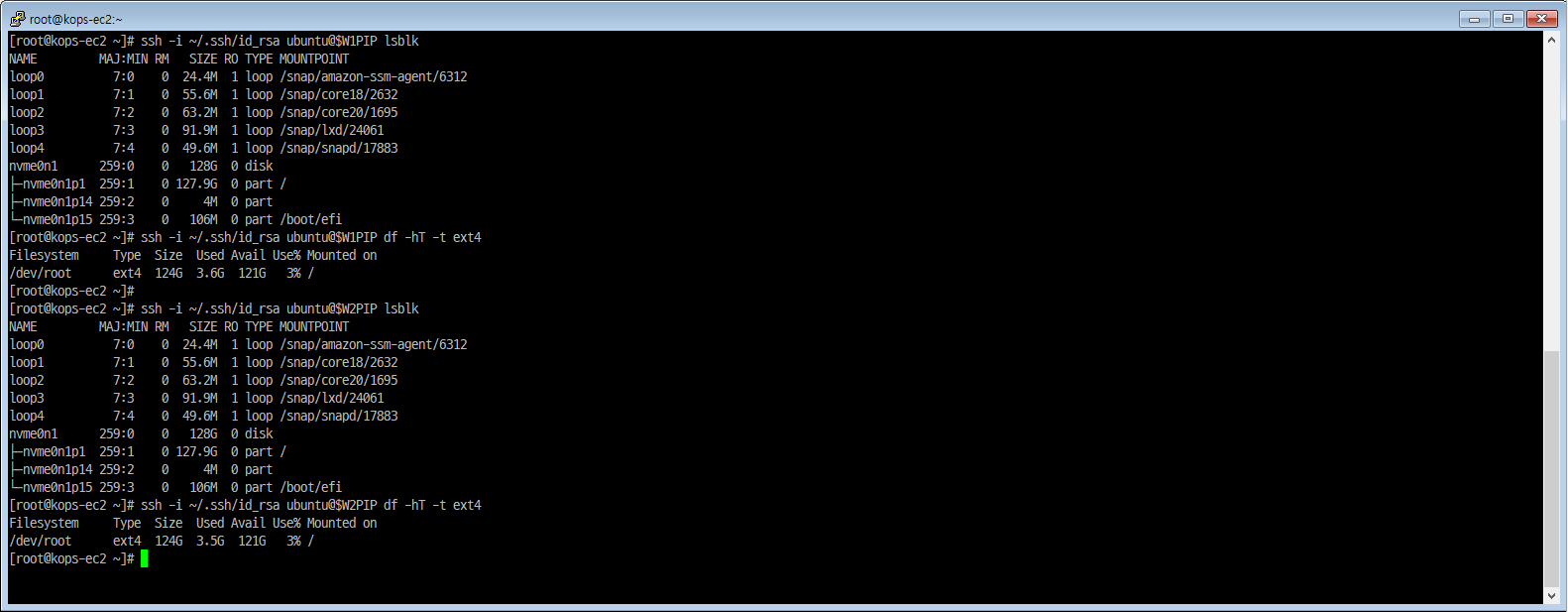
[worker node] 스토리지 확인
|
|
[worker node-W1PIP] node EC2 메타데이터 확인
|
|
|
|
|
|
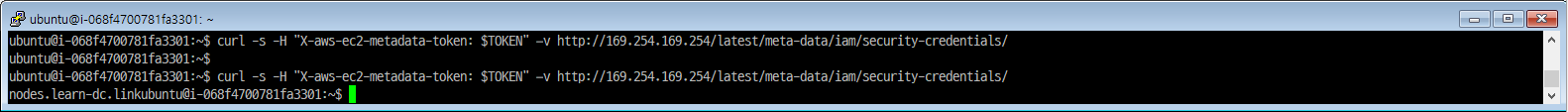
|
|
2. Helm 실습
워드프레스 배포
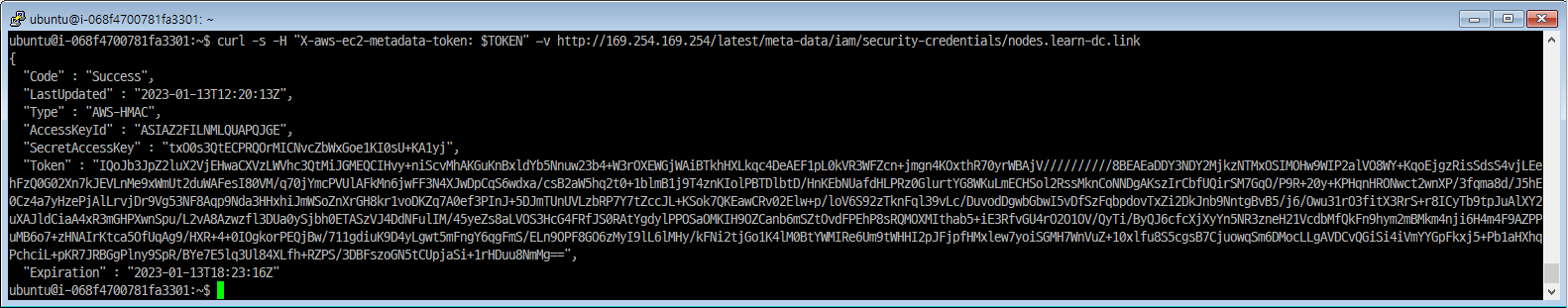
아티팩트 허브에서 검색
|
|
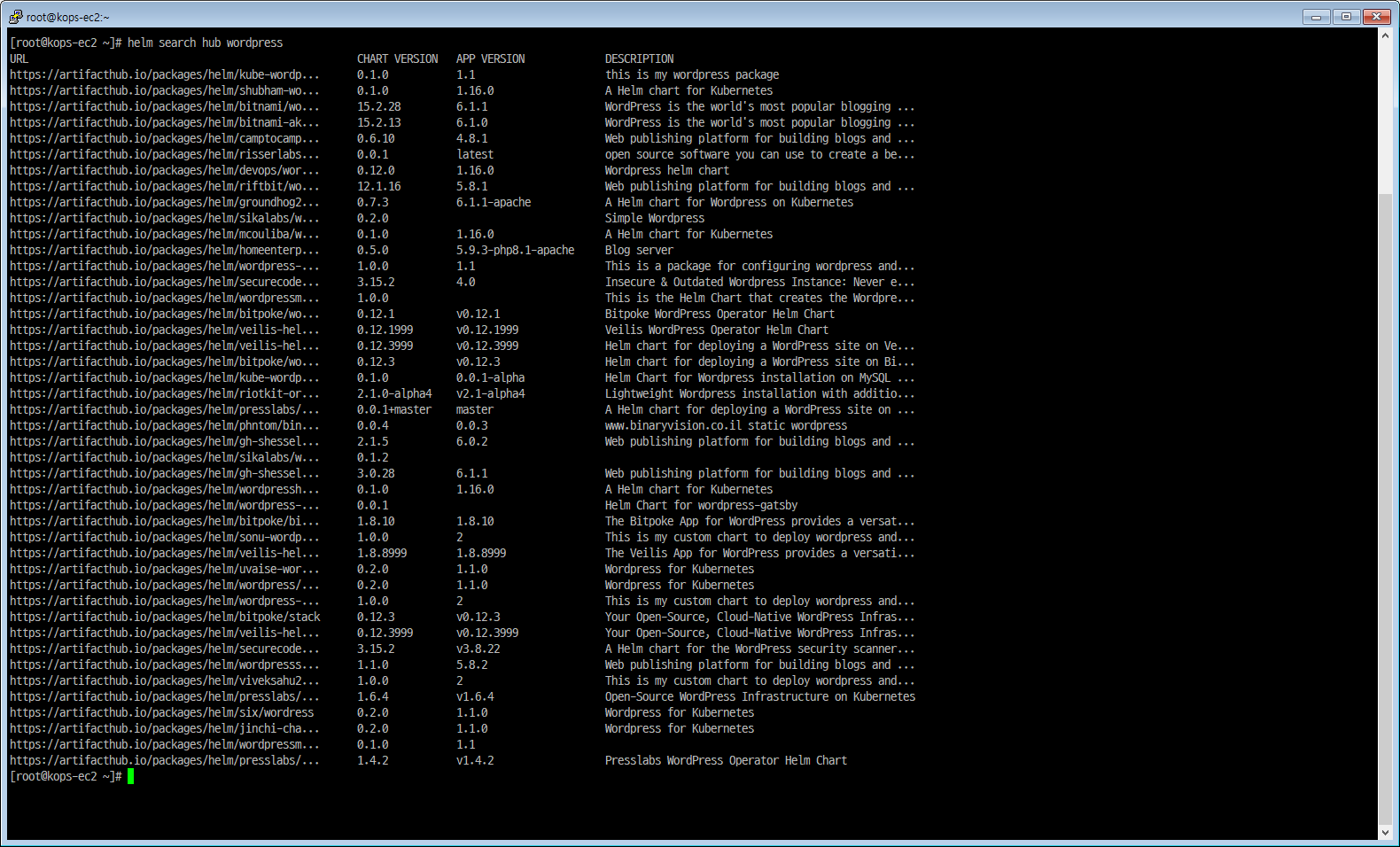
Repo
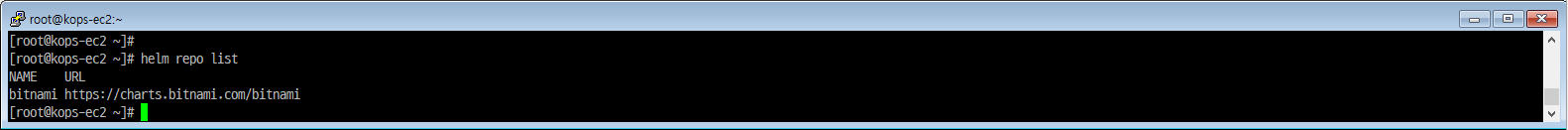
repo 추가 및 확인
|
|
|
|
wordpress 설치 - 파라미터 지정
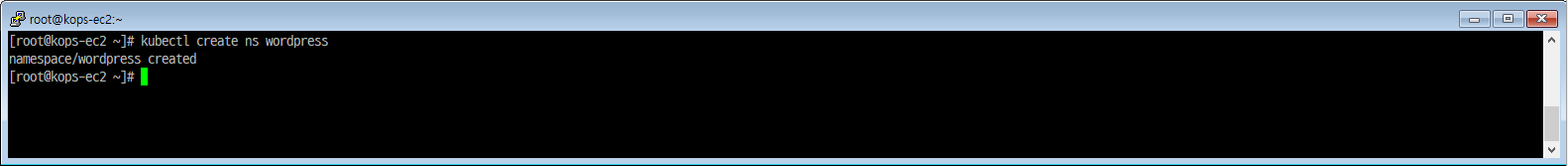
네임스페이스 생성
|
|
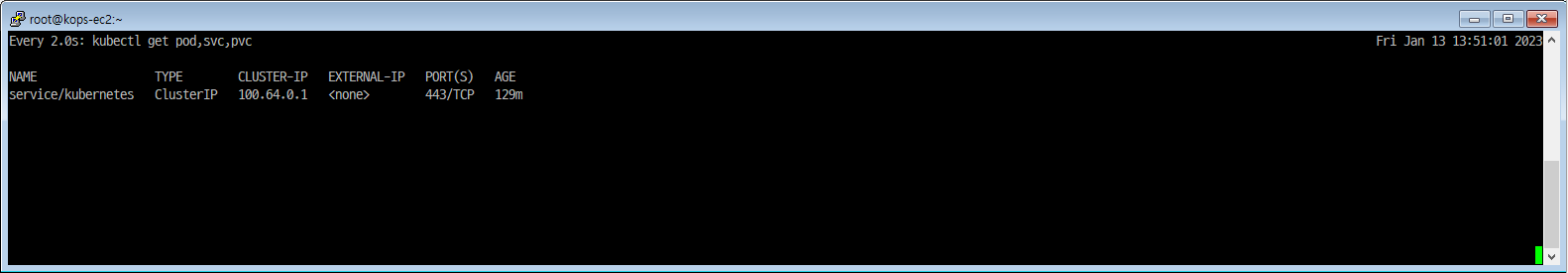
터미널2 모니터링
|
|
기본 파라미터를 덮어쓸 수 있게 --set 으로 지정
|
|
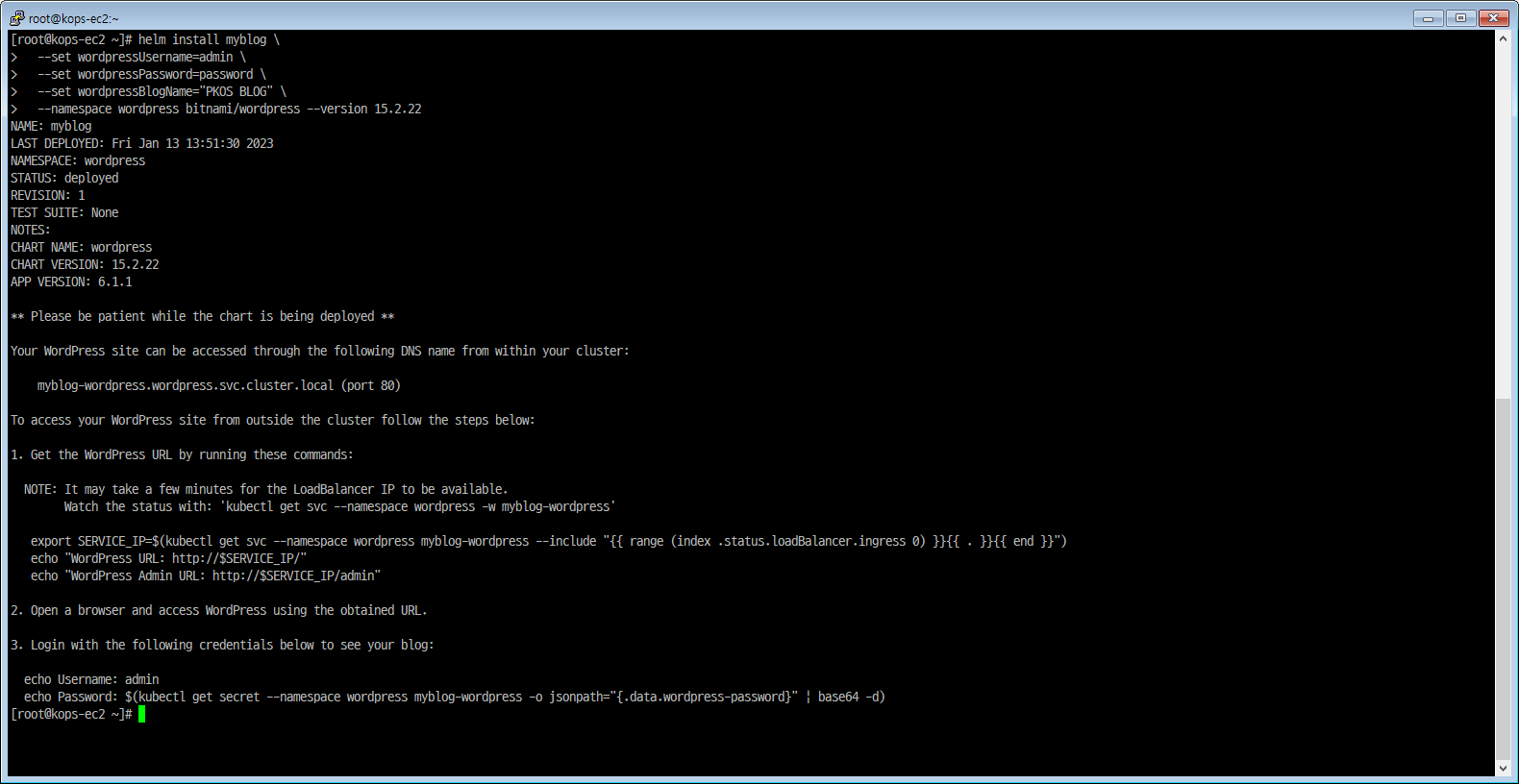
wordpress 네임스페이스로 변경
|
|
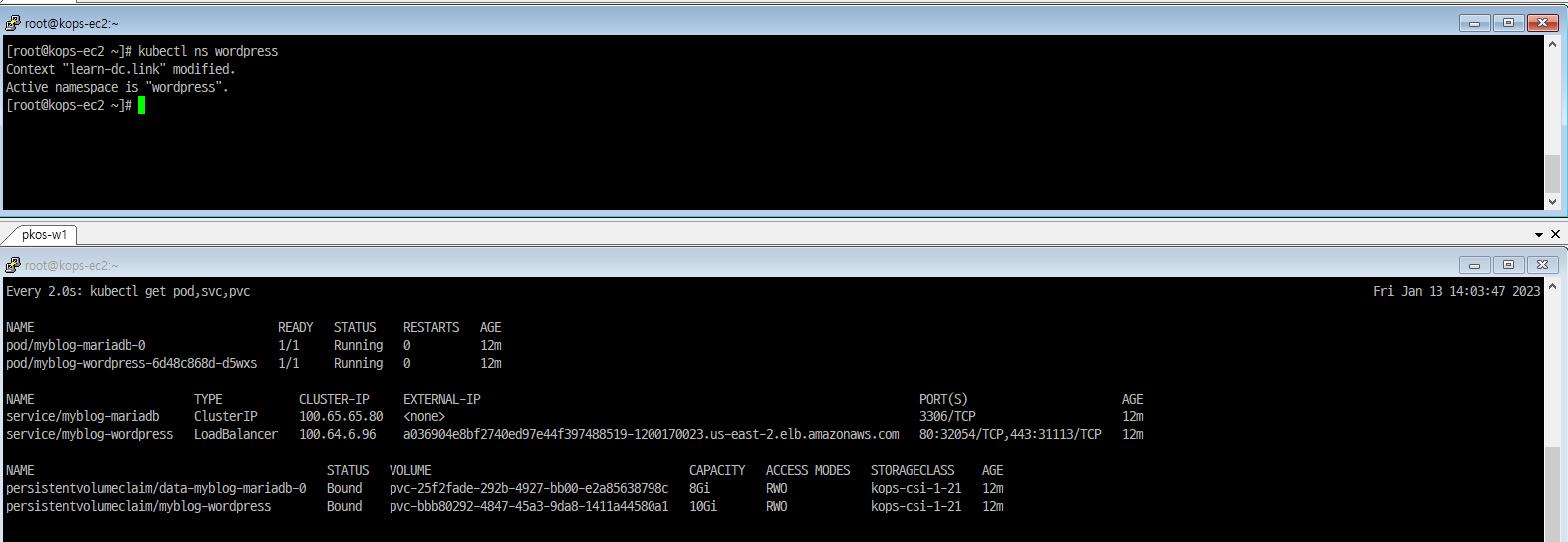
설치 확인
|
|
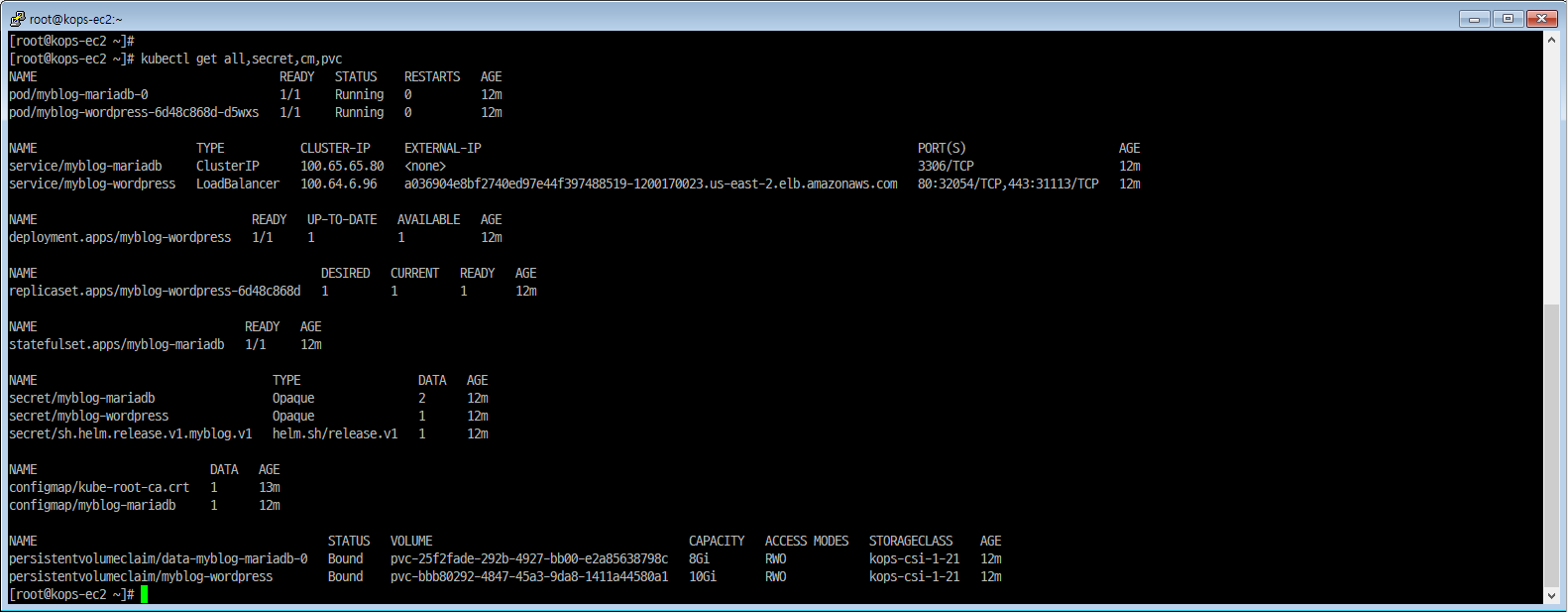
|
|
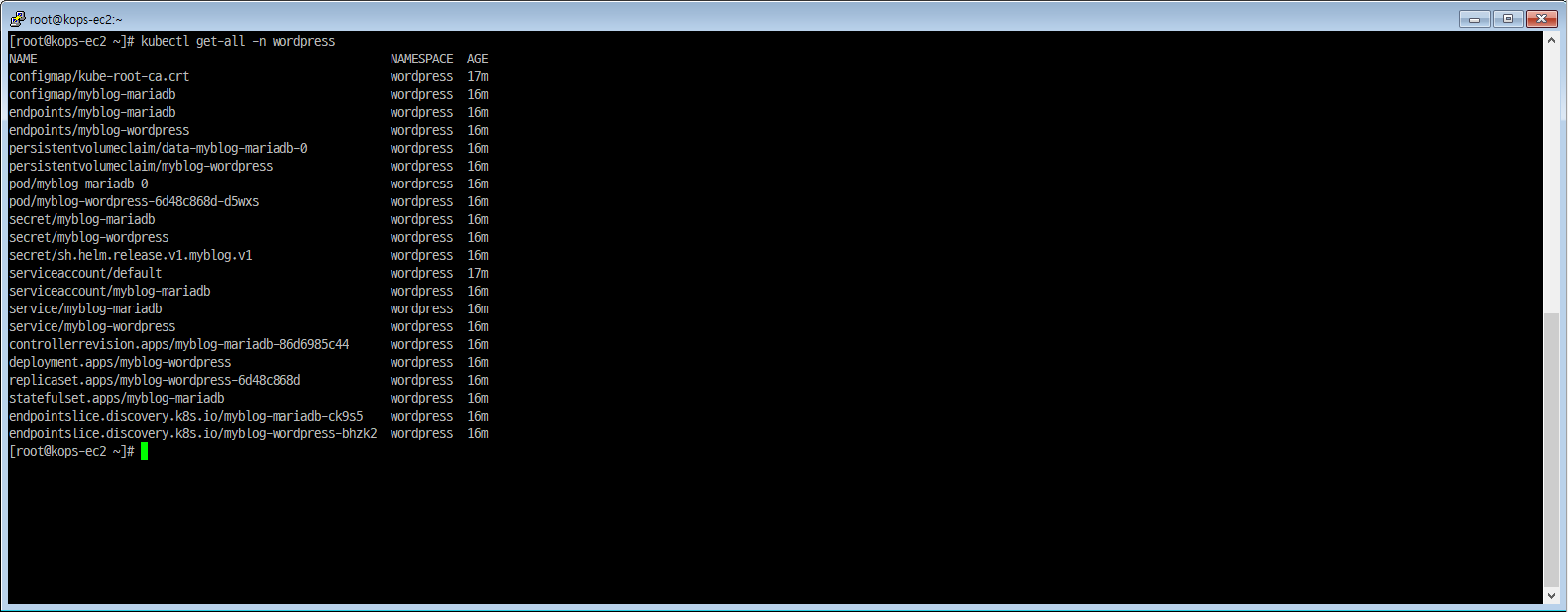
|
|
wordpress 접속
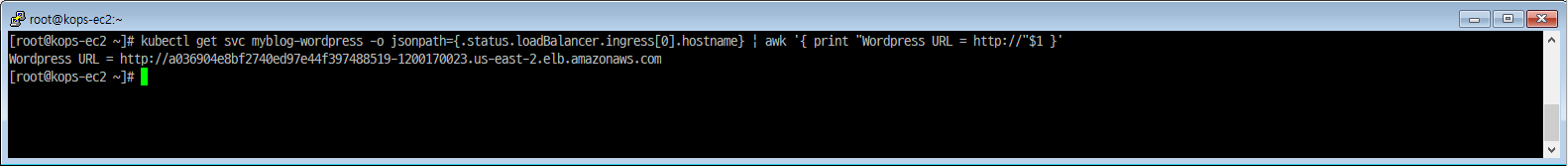
wordpress 블로그 접속 : CLB 주소로 웹 접속
|
|
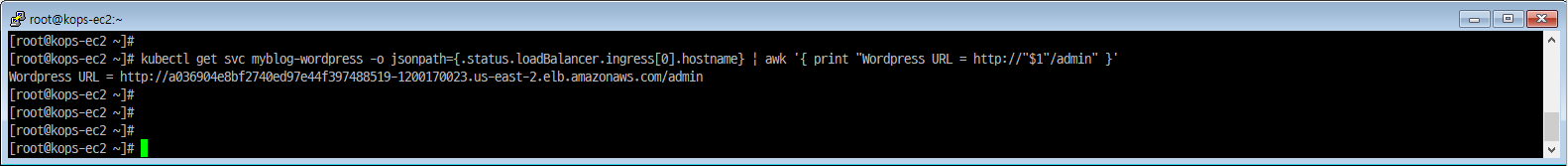
wordpress 블로그 관리자 페이지 접속 : CLB 주소로 웹 접속
|
|
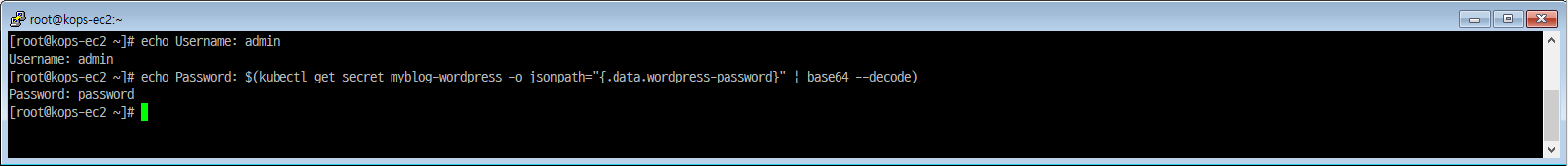
관리자 계정(admin 페이지) 정보 확인
|
|
관리자 페이지 접속 및 로그인
관리자 페이지 접속 후 post 작성
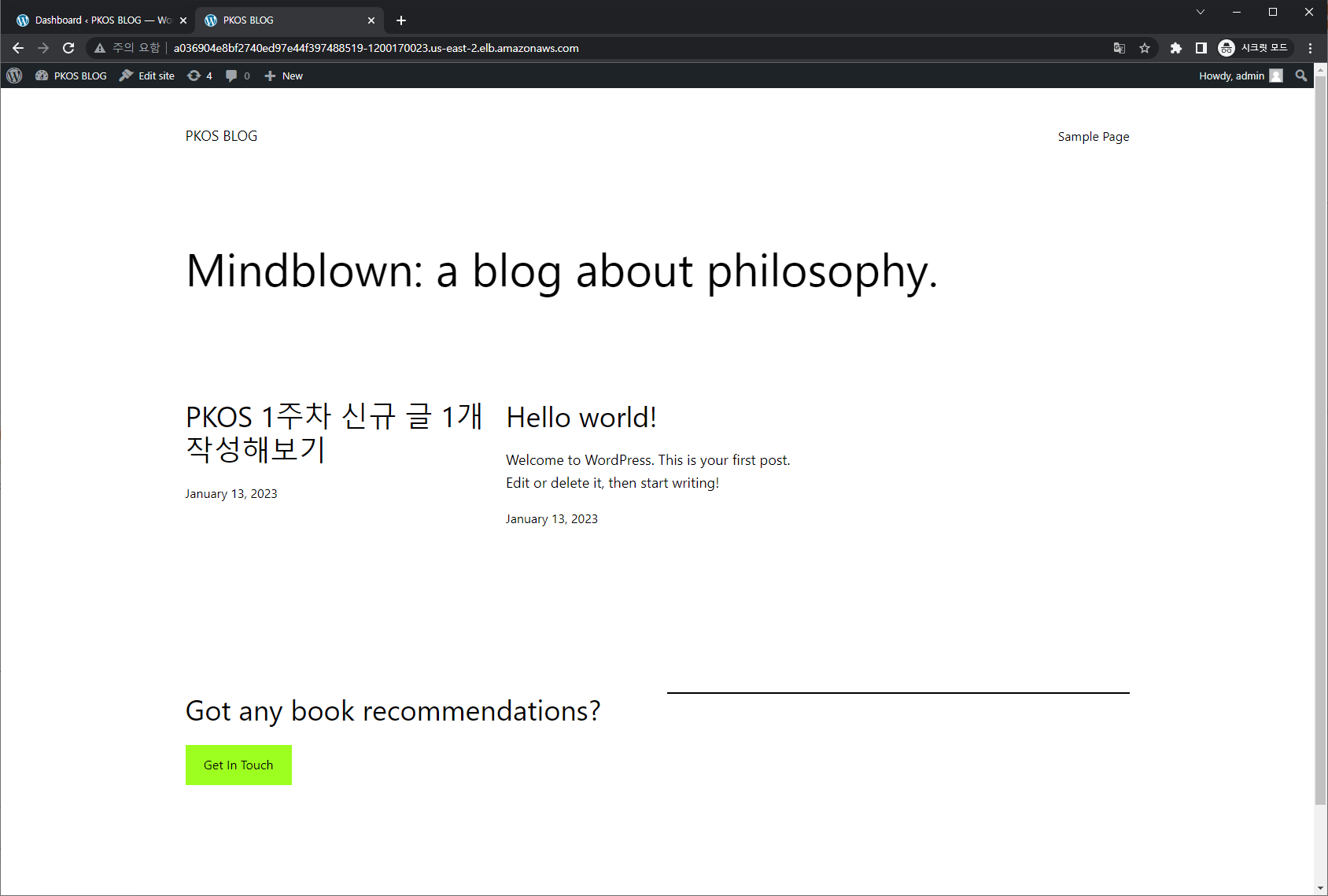
끝.
1: “Classic Load Balancer 마이그레이션” Elastic Load Balancing 사용설명서(AWS). 2023.01.12 접속. https://docs.aws.amazon.com/ko_kr/elasticloadbalancing/latest/userguide/migrate-classic-load-balancer.html